Non-human identity management: How to govern what you can’t see or classify

Julissa Caraballo
Principal Product Marketing Manager, Axonius

The way organizations manage and think about identity has changed forever. It’s no longer just human users tethered to Active Directory. Today, the majority of identities belong to non-humans: service accounts, bots, cloud roles, API tokens, and autonomous agents. They don’t use passwords. They don’t take security training. Yet they often hold more privilege than human users.
As SaaS, automation, and AI adoption accelerate, these non-human identities (NHIs) are multiplying fast. And because they’re rarely tracked, updated, or governed, they create a growing attack surface. Most security teams know the risk, but they’re missing one thing: trustworthy data to actually do something about it.
We believe non-human identity management isn’t just another box to check in IGA. It requires a new foundation: one rooted in real-time data, continuous behavioral analysis, and enforcement that adapts to how identities behave in practice, not how they look on paper.
Why non-human identities are increasingly difficult to govern
Human users are easy to trace. HR onboards them. IT provisions them. Offboarding eventually shuts them down. NHIs don’t follow that script. |
Developers spin up service accounts for CI/CD pipelines. Cloud teams generate temporary roles to run background processes. These identities often bypass joiner-mover-leaver processes, making them both hard to discover and even harder to govern.
Legacy IGA platforms make things worse by treating identities as static rows in a table. They pull data from a handful of sources once a day. But an AWS token or a GitHub automation doesn’t wait for nightly syncs. Even when it shows up, those tools can’t tell if it’s a developer account or a background service. Without behavior data and real-time classification, they’re blind.
This is where you need real-time visibility and behavioral context, and where Axonius Identities helps you finally govern what legacy tools can’t.
How to take a data-first approach to non-human identity management
Axonius Identities is rooted in a data-first philosophy: you can’t govern what you can't accurately see and contextualize. |
Our platform integrates with hundreds of data sources, identity providers, SaaS apps, cloud platforms, endpoint tools, directories, and HR systems to provide you with a unified view of real-time identity artifacts.
But we don’t stop at correlation. We:
Normalize, de-duplicate, and enrich identities with behavioral telemetry.
Classify NHIs by behavior, not just by labels.
Track entitlements and actual usage, showing the difference between permissions granted and permissions exercised.
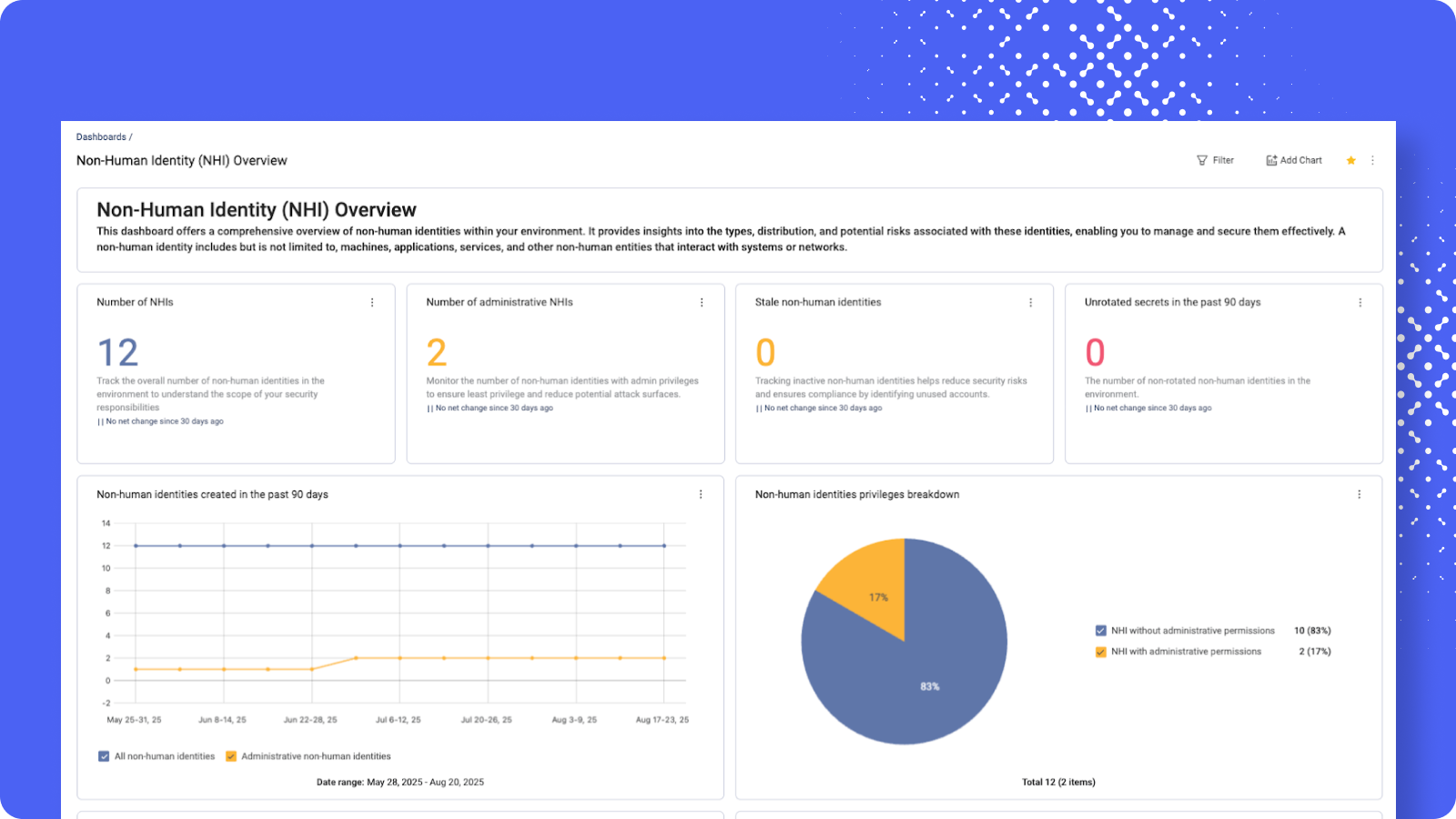
Track total NHIs, detect unused accounts, identify administrative privileges, and surface secrets that haven’t been rotated. Visibility like this turns potential risks into actionable insights.
By analyzing usage patterns, you can automatically spot identities that behave like machines: accounts that initiate scripted API calls, never log in interactively, or run on a set schedule. Even if a service account is mislabeled in the directory, or not listed there at all, our platform surfaces and categorizes it correctly based on what it does, not what it was called.
And we go deeper. Our adapters reveal not only what permissions an identity has, but which ones are actually being used. While the depth of this visibility depends on the integration each application provides, the utilization data we already extract offers far more clarity than static entitlement inventories alone.
As a result, your identity team can finally distinguish dormant access from essential access, identify over-scoped NHIs, and reduce blast radius by removing unused entitlements, all critical steps to enforcing true least privilege across complex environments.
How to move from static governance to IVIP
Gartner recently coined the term Identity Visibility and Intelligence Platforms (IVIP), defining a new category of solutions that move beyond static governance. IVIP correlates identity data across all systems and continuously analyzes it to surface risk, enforce policy, and validate posture.
Axonius Identities is IVIP at its core:
Continuous visibility across human and non-human identities in hybrid and multi-cloud environments.
Classification that separates interactive users from programmatic agents, regardless of labels.
Dynamic governance powered by real-time usage data, not stale provisioning records.
The critical difference comes down to timeliness and trust.
Legacy IGA tools assume that if an account was approved six months ago, it’s still valid. With Axonius Identities, you’re never left relying on assumptions. |
You can use our platform to continuously track when an account was last used, what it did, which permissions it exercised, and whether those actions align with policy. By pulling and correlating identity data across providers, HR systems, SaaS apps, infrastructure, and cloud platforms, Axonius gives your team the context to classify identities and govern them in real time.
That’s the heart of IVIP: not just cataloging identities, but governing them with confidence and context.
Addressing the limits of static governance with behavior data
Traditional governance models were built for people. They assume identities are onboarded through HR and eventually offboarded when employment ends. Non-human identities follow none of those patterns. |
They’re created ad hoc, by developers, scripts, integrations, and third-party tools, often with no ownership or documentation. They rarely get cleaned up. And over time, they tend to accumulate excessive privileges, either by convenience or misconfiguration.
A service account created for one narrow task might inherit broad admin rights simply because it was cloned from another template, or because no one knew the exact minimum access it needed. Left ungoverned, these accounts persist indefinitely, quietly introducing risk with every overlooked permission and connection.
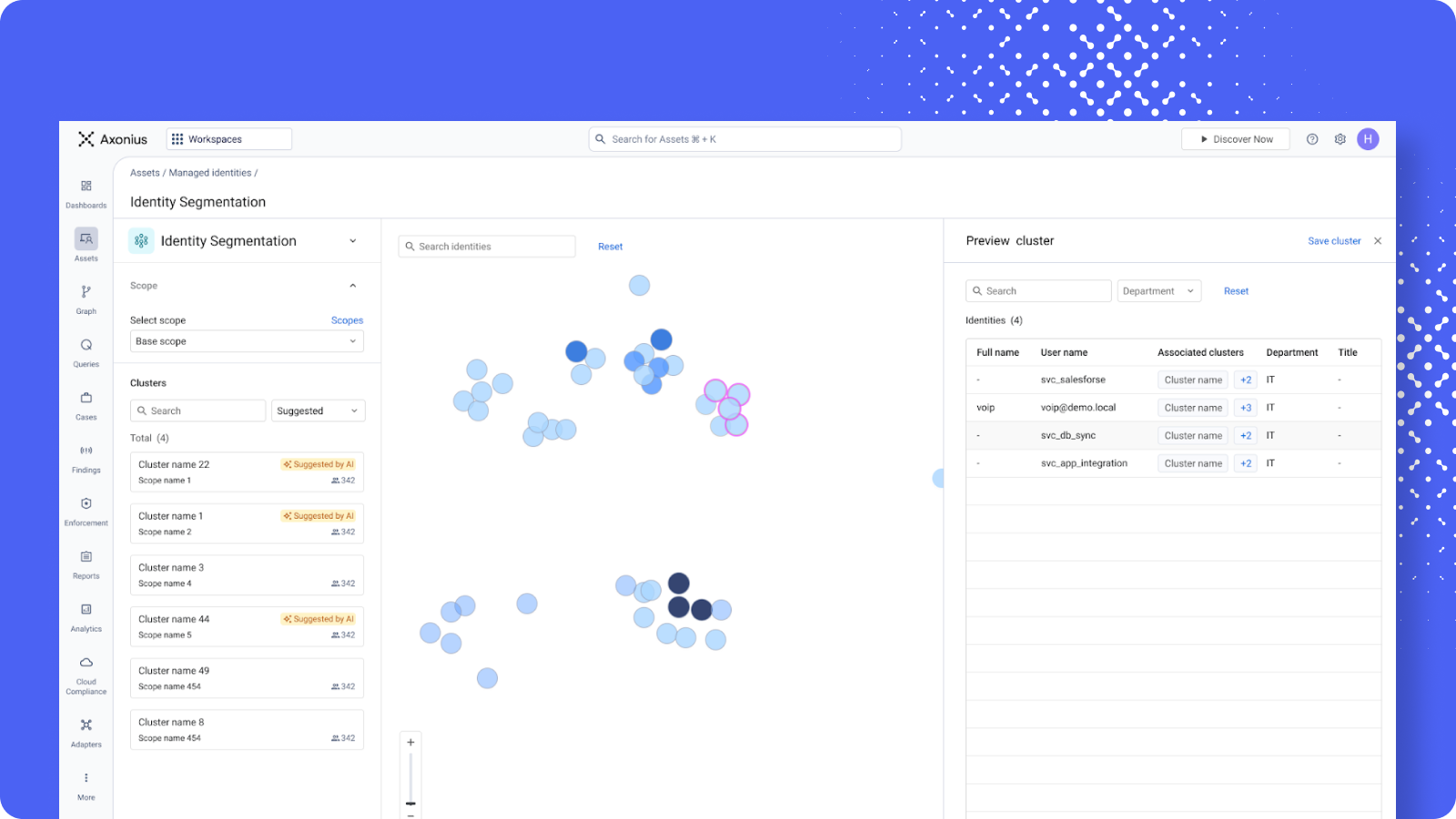
Visualize identity clusters across your environment with automated, behavior-based segmentation. Whether it’s service accounts or integration users, group identities by role or activity to uncover anomalies fast.
That’s why governance has to be behavior-driven. With Axonius Identities, your team can move past static entitlement reviews.
You can finally answer the questions that matter most:
- Who owns this account?
Is it actually being used, and by whom?
Which services or users interact with it?
From which IPs is it accessed?
If we apply an IP-based filter tomorrow, will it break a critical automation, or will it have no effect?
Axonius continuously surfaces this context in real time, enriched with ownership, activity, dependency mapping, and access-source intelligence. That allows your team to understand the operational impact before making changes, and to automate remediation when it’s safe to do so.
The result is a holistic view of non-human identity risk: dormant or misused accounts are flagged, toxic combinations detected, and unused entitlements removed, often without manual intervention. Static governance was never built for this level of complexity. Axonius is.
How to turn identity events into actionable signals
One of the most powerful features of Axonius Identities is how it shares context-rich events with the teams who need them. For example, if a previously dormant API token suddenly accesses a high-risk application, you can surface that event with full context:
What the identity is (machine, service, or bot)
Where it originated
What permissions it used
Whether that behavior is consistent or anomalous
What systems it touches across your identity graph
Where most tools treat identity risk as a compliance checkbox, Axonius treats it as a live operational signal. |
And you don’t have to hunt for context in a dashboard. It’s delivered to the right places, from SIEM alerts to certification reviews to automated workflows, so you can act immediately.
Preparing for the future of non-human identities
The next wave of NHIs won’t be just service accounts. It will be autonomous agents and policy-driven cloud roles that exist for seconds at a time.
Governing them requires an approach that is:
Continuous, not point-in-time
Behavior-aware, not label-based
Event-driven, not workflow-centric
Axonius was built for this reality. Our architecture scales across diverse environments and adapts to constant change. |
We combine real-time telemetry, identity normalization, behavioral classification, and cross-platform policy enforcement to deliver governance that’s dynamic, distributed, and data-driven.
Move from oversight to enforcement with Axonius Identities
Non-human identities are the new privileged users. And in many organizations, they already outnumber humans. Trying to govern them with spreadsheets and quarterly reviews is dangerous.
With Axonius, you can make oversight operational. We don’t just show you identities, we help you act: remove unused entitlements, deprovision stale or orphaned accounts, and assign ownership automatically.
Let’s govern what matters. Even if it’s not human. Request a demo of Axonius Identities.
Categories
- Identity

Get Started
See how to make asset intelligence actionable with a guided demo:
- Stop chasing data — work from one asset model your entire team can trust.
- See what's exposed before it's a problem — surface coverage gaps automatically.
- Turn alert noise into action — cut thousands of alerts down, to the ones that matter.
