AXONIUS PLATFORM
Software Assets
Comprehensive, actionable visibility into software risk and usage across the organization – empowering Security and IT teams to build, manage, and enforce a software policy program.
The world’s top companies rely on Axonius
Gain clarity and take action over every piece of installed software
Axonius Software Assets eliminates manual, outdated assessments by automatically inventorying software across all devices, managed or unmanaged. With a unified view and deep context – like major and minor versions, End-of-Support and End-of-Life metadata, user ownership, vulnerabilities, and risk levels – teams can confidently optimize security, reduce risk, and streamline operations.

Track Risky Software
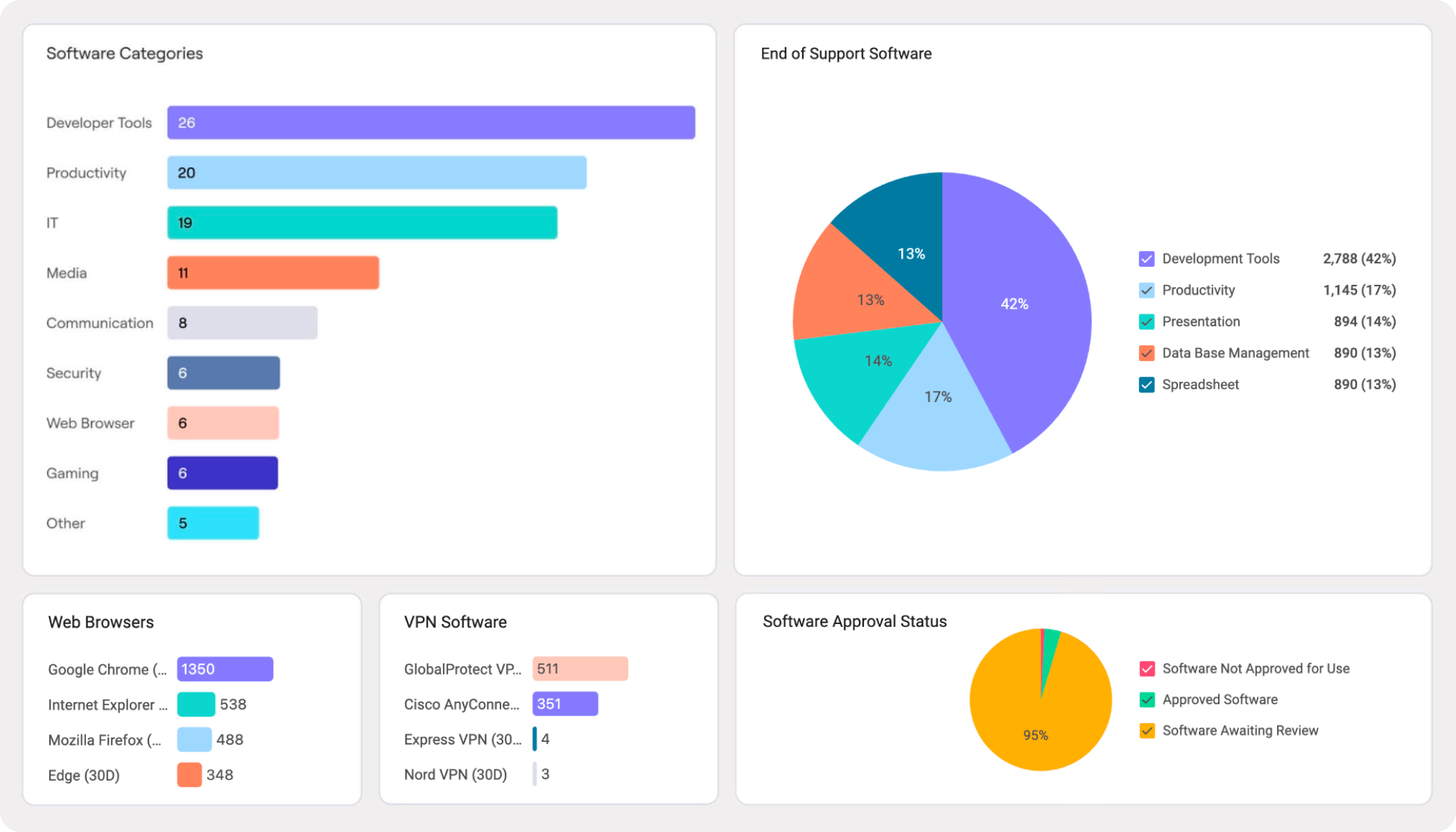
Manage software risk across the enterprise
Rapidly identify risky software, including packages that are past their End-of-Support or End-of-Life dates, as well as Shadow software on both managed and unmanaged devices, without the need for agents or scanners. Automatically open tickets for operations teams, or directly update software packages via the Axonius Enforcement Center.

Unified Software Catalog
All your software, aggregated and accurate
Correlate software data from all your tools into a single, reliable inventory. Axonius aggregates data from sources like EDR, endpoint management, and vulnerability assessment tools to deliver a complete inventory of unique applications – no agents or network scans required.

Investigate Usage and Hygiene
Get answers to your software questions without the guesswork
Pinpoint where software is installed, who has access, and its criticality to your environment. Track specific insights in the software Registry, and ensure that application usage stays compliant with business requirements while not being over-provisioned or under-utilized.

Enforce Approved Software
Discover and remediate unapproved software
Maintain an authoritative list of Approved and Unapproved software titles and versions, making detection of unapproved software as easy as running a query once, and saving it for automatic and continuous monitoring. Ensure that Unapproved software is either escalated for review, or remediated out of the environment, reducing risk and maintaining compliance.
Ready to act on managing your software estate?
Schedule a personalized demo with an Axonius specialist.
Key Differentiators
Software risk lives across your attack surface - and that's how Axonius sees it all.

No blind spots, no agents
Unlike other tools that require agents or scans, Axonius aggregates data directly from your existing systems to deliver a complete and accurate software inventory with zero disruption

Software insights in full context
Axonius doesn’t just inventory software—we integrate device, user, and vulnerability data to provide a richer, more actionable understanding of your software assets.

Full lifecycle automation
While others stop at discovery, Axonius tracks the full software lifecycle, enabling you to manage applications from deployment to decommissioning without the complexity of point solutions.

Turn visibility into action
Axonius combines visibility with powerful workflows, enabling immediate action to remediate risks, reduce costs, and align software with compliance policies—all from a single platform.
Customer stories
Customers of all kinds and sizes trust Axonius to secure their software assets
Loading carousel...

Platform
The Axonius Asset Cloud
Axonius is where posture, management, and operations converge across your core cybersecurity programs – all backed by our market leading asset intelligence.

See Axonius in action
See how to make asset intelligence actionable with a guided demo:
- Stop chasing data — work from one asset model your entire team can trust.
- See what's exposed before it's a problem — surface coverage gaps automatically.
- Turn alert noise into action — cut thousands of alerts down, to the ones that matter.
















