Axonius for CTEM: From validation to mobilization

Editor’s note: The article below is adapted from our guide, Axonius for CTEM. You can view the full guide online for free here. |
Continuous Threat Exposure Management (CTEM) is a strategic approach to discovering and managing cyber risks, offering a pragmatic, always-on path to identifying, prioritizing, and mitigating threats.
We’ve covered the fundamentals before (see our intro to CTEM here), but now it’s time to roll up our sleeves.
In this excerpt from our full guide, Axonius for CTEM, we break down how to put the last two critical steps of CTEM into action with the Axonius Asset Cloud — helping you tackle exposures across your entire infrastructure.
CTEM step 4: Validation
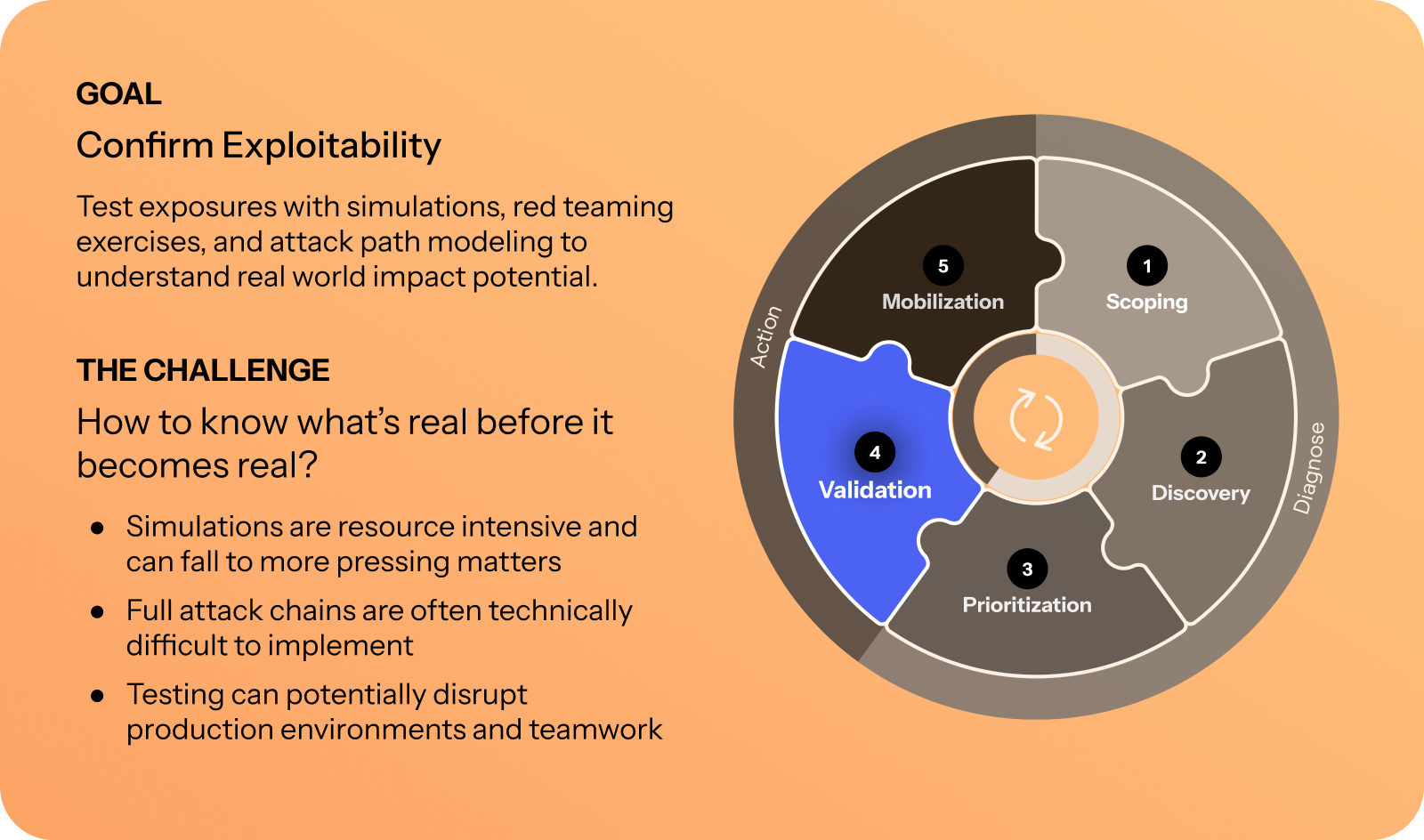
Validation with Axonius
While Axonius does not support native validation capabilities like Breach Attack Surface (BAS) or Pentest as a Service, the platform automates the start and coordination of the validation process through workflows.
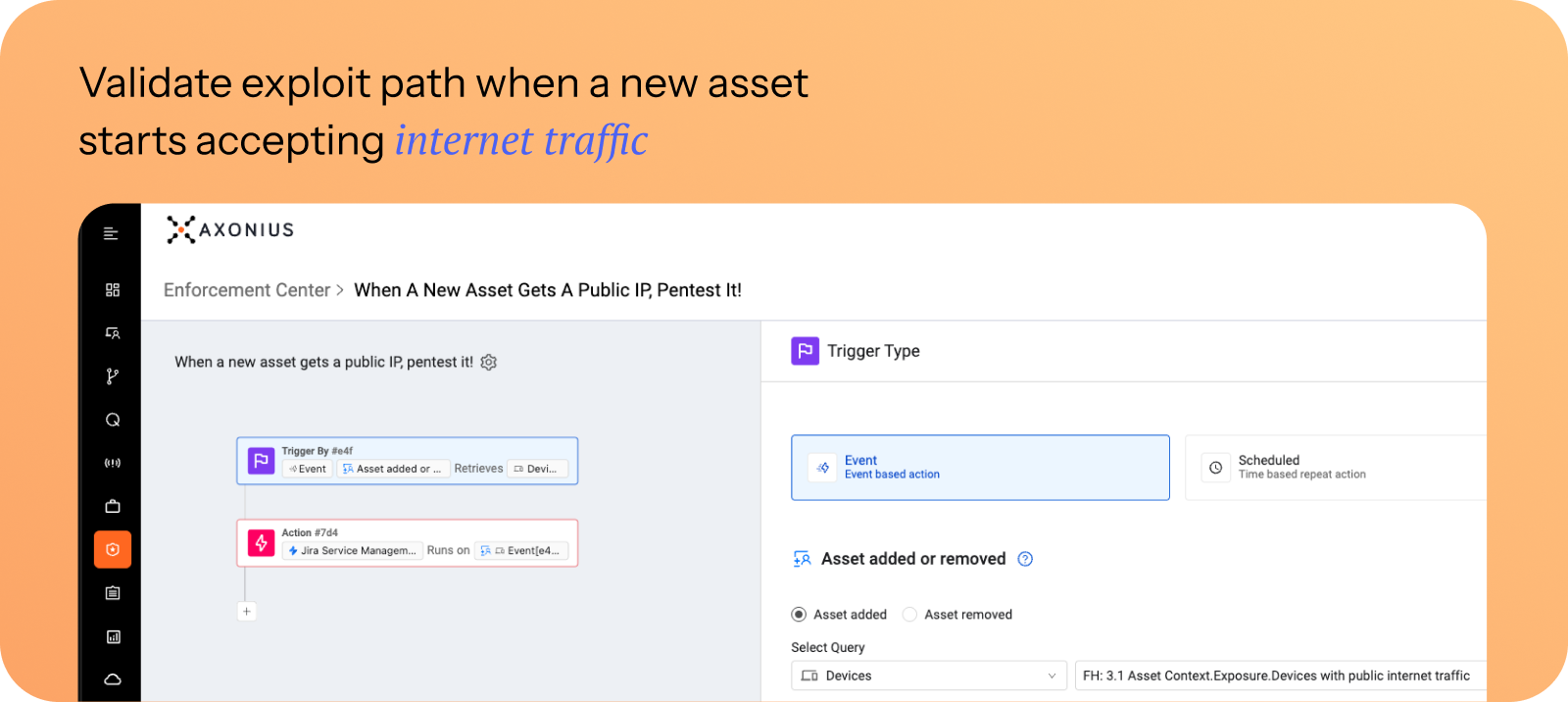
Workflows
Axonius Workflows helps organizations automate actions whenever assets or exposures meet a condition. In the context of validation, workflows can be used for triggering a task run in your Breach and Attack Simulation (BAS) service for an automatic pen test or opening a ticket with your red team for manual pen testing with the targeted asset or exposure.
At Gerson Lehrman Group, Axonius helped IT and security teams move away from siloed spreadsheets and tools, replacing them with shared dashboards. Validation signals from CrowdStrike deployments or AWS instances could now be tracked centrally, ensuring faster handoffs across teams. |
Adapters
In the context of validation, Axonius adapters can confirm the completion of validation tasks from your red team and BAS services. Like any other data in Axonius, data like exploit confirmations can be used across queries, risk prioritization, and to drive mobilization.
Adapters can be used to bring confirmation signals not only from your own infrastructure (BAS tools) but also from other sources like Threat Intelligence Feeds.
CTEM step 5: Mobilization
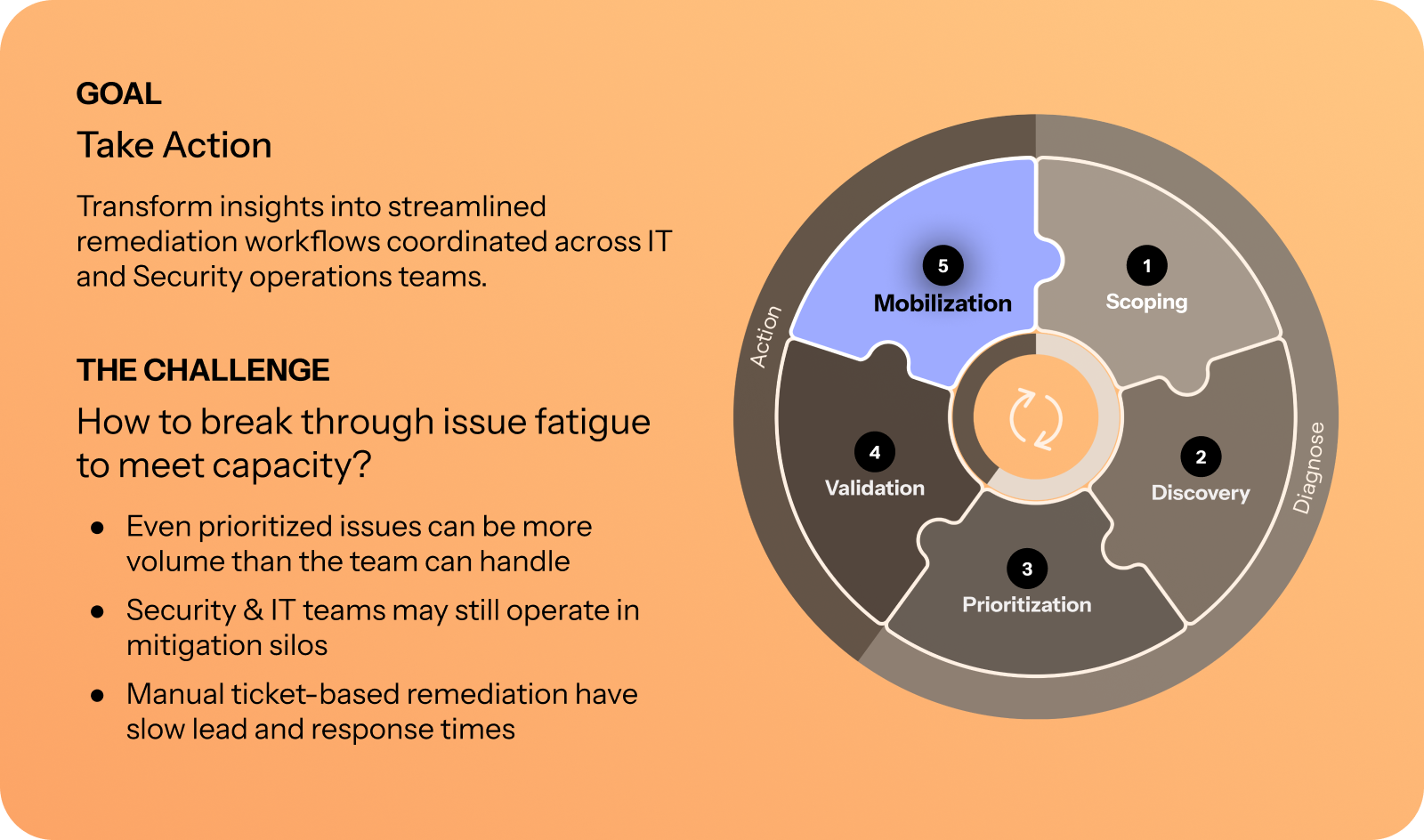
Mobilization with Axonius
Axonius supports mobilization by identifying owners, triggering mobilizations through automation and tickets, tracking the remediation process, and validating if a remediation is effective.
Axonius delivers mobilization through data, actions, workflows and enforcements, case management with ticket binding, and continuous Scoping and Discovery.
At BlueLinx, security teams replaced spreadsheet-driven reviews with automated enforcement actions powered by Axonius. By identifying exposures and triggering remediation workflows in real time, they shifted from reactive firefighting to proactive exposure management. |
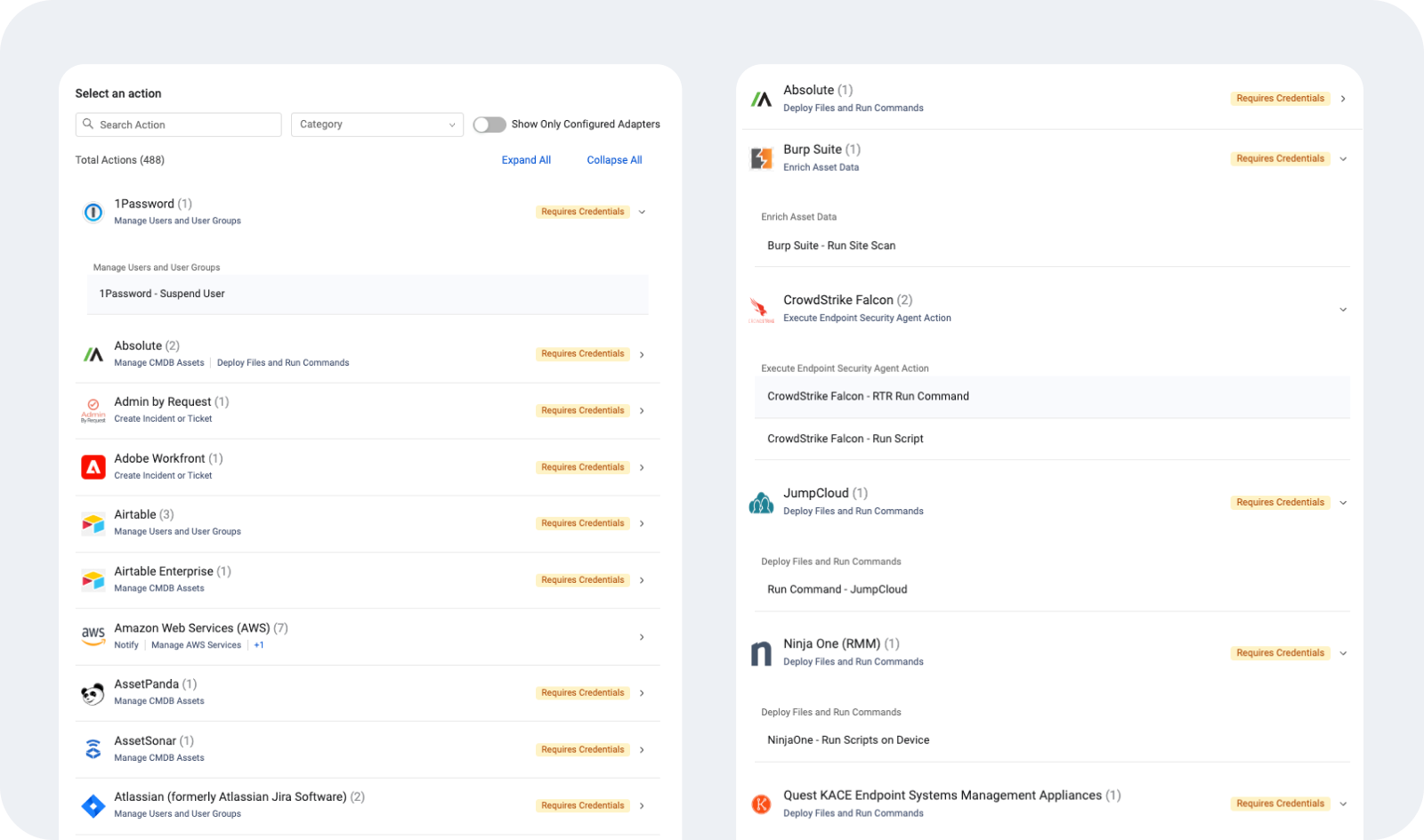
Enforcement Actions
Enforcement Actions are API-based integrations provided by Axonius to perform tasks in third-party systems.
In the context of Mobilization, Enforcement Actions are used either to automatically remediate third-party systems — for example, by remotely patching a workstation, deprovisioning a user, quarantining or isolating a laptop, or turning off a virtual machine — or to notify and mobilize teams to manually remediate exposures, typically through alerts, notifications, or tickets.
Workflows and enforcements
Workflows and enforcements act as a trigger for mobilization in Axonius. By using queries or other triggers, you can define when the mobilization will happen and what actions should be performed. Enforcements provide a simple and easy way to mobilize. It’s great for simple actions and can be triggered not only automatically, but also directly from the Axonius interface when a specific asset or exposure requires immediate mobilization.
Workflows are a new feature within the Axonius platform that expands enforcements with no-code, allowing you to add your own logic to the mobilization. Workflows work well when you need to change action based on logic — i.e., deploy an EPP agent only if the asset can receive remote commands via SCCM/MECM. Otherwise, open a ticket for manual remediation.
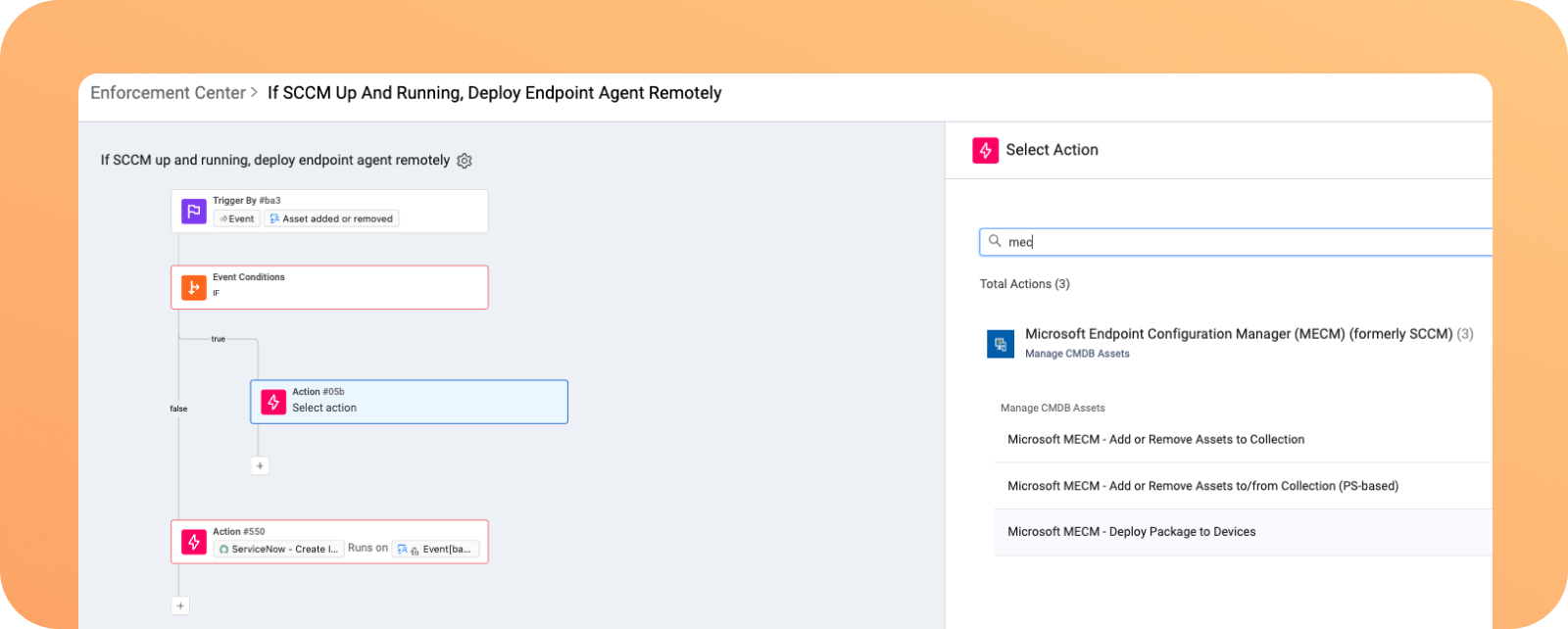
Workflows can also be triggered by events external to Axonius, such as when a Slack message is received, an employment status change in HR, or a critical event is triggered by other solutions in your stack.
Case management and ticket binding
Case management and ticket binding serves as a trigger in Axonius for when you need to mobilize other teams across your organization through their ticket system of choice.
Whenever a query is triggered, it uses your defined policy to mobilize the right team and ticket system — i.e., SRE team and PagerDuty, Internal IT and ServiceNow, Engineering and Jira, decide what ticket operation will be executed — i.e., create a new ticket or update an existing one, and create a case in Axonius to keep track of the ticket execution against your security MTTR and SLAs.
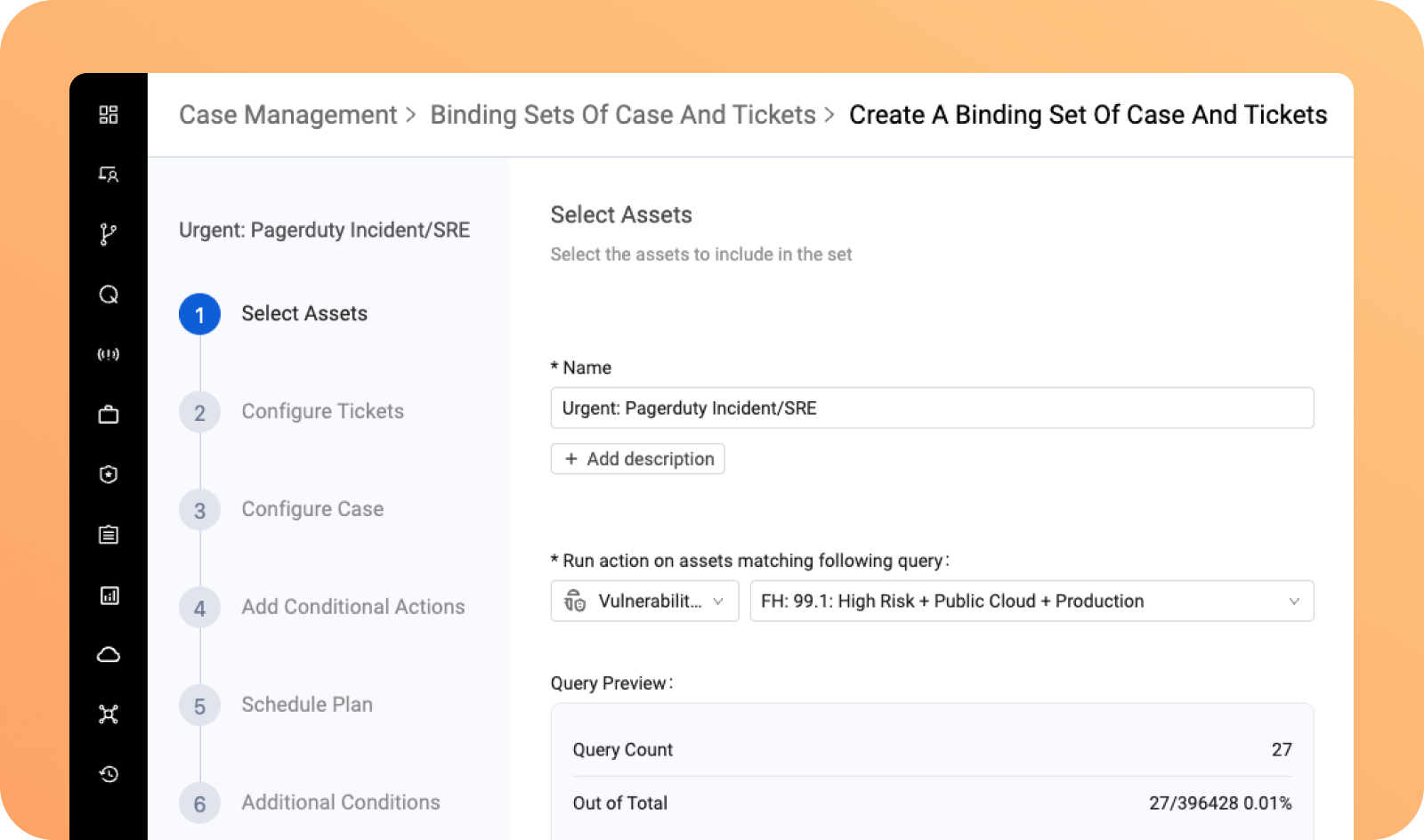
As the ticket progresses, Axonius keeps track of what assets and exposures are fixed and the status of the associated ticket across different teams.
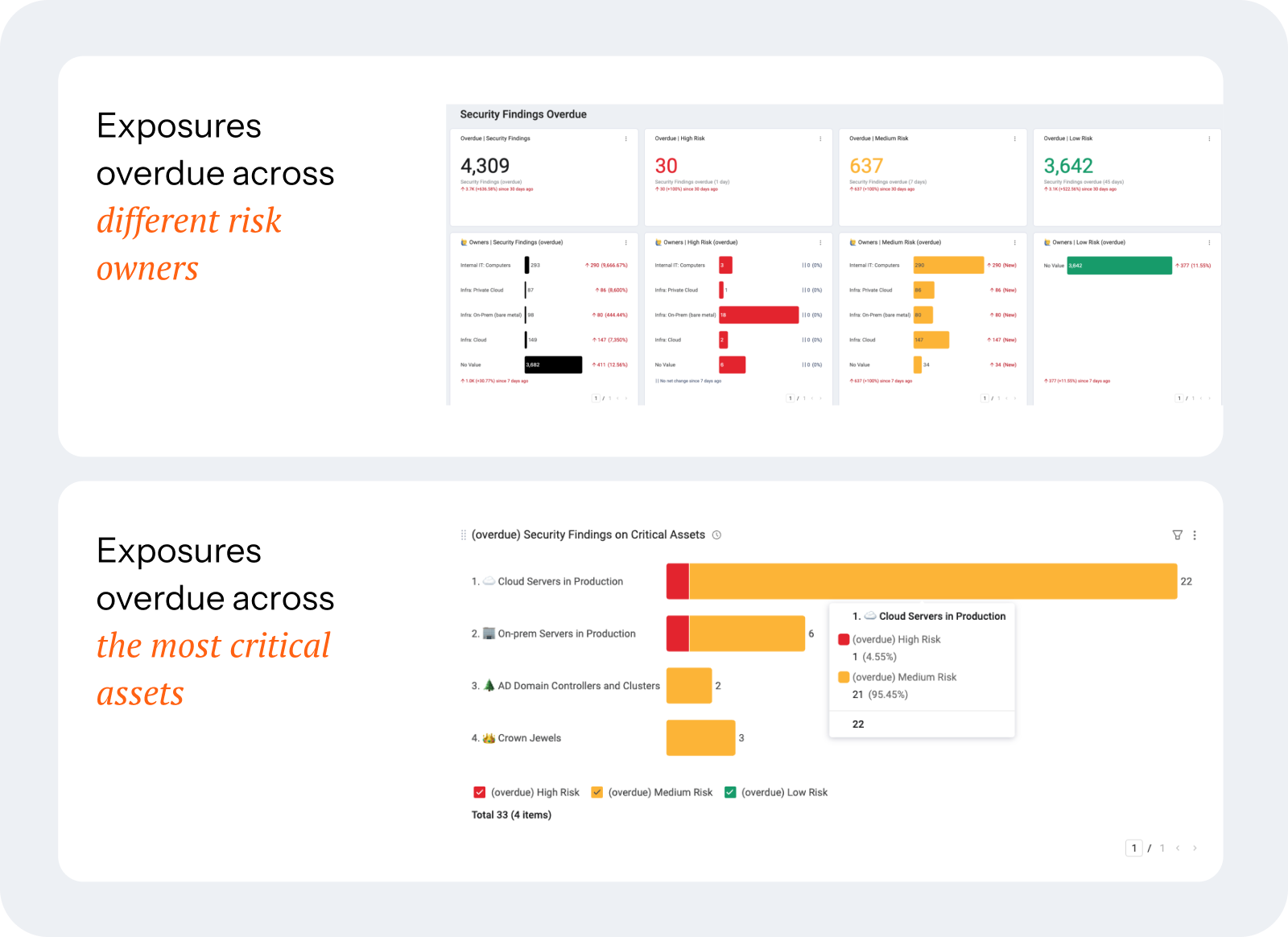
Through ticket adapters and dashboards, Axonius can continuously track the ticket progress and highlight tickets and cases overdue across different teams:
Stop planning. Start doing CTEM.
Download our Axonius for CTEM eBook and learn how to:
Navigate the five core stages of a CTEM program: scoping, discovery, prioritization, validation, and mobilization
Configure the Axonius platform to support CTEM across your entire environment
Launch your program with quick wins, meaningful momentum, and continuous improvement
Already feeling inspired? Get a product demo or talk to our team and see how Axonius can help you put CTEM into action.
Categories
- Threats Vulnerabilities

Get Started
See how to make asset intelligence actionable with a guided demo:
- Stop chasing data — work from one asset model your entire team can trust.
- See what's exposed before it's a problem — surface coverage gaps automatically.
- Turn alert noise into action — cut thousands of alerts down, to the ones that matter.
