How Epiq built a foundation of organizational visibility with Axonius

A worldwide provider of legal services, Epiq serves law firms, corporations, financial institutions, and government agencies. With over 80 offices and 17 data centers spread across different continents, Epiq has transformed the business of law for its clients globally for nearly two decades.
Key Challenges
Needing to secure unknown agents and devices while maintaining security
Managing assets and systems across complex environments
Conglomerating information into one simple place and giving visibility to multiple teams
Conglomerating assets across environments
Epiq is a full-service legal technology provider that works with litigation firms and corporate legal departments to guide clients through everything from bankruptcy management to class action lawsuits or even corporate restructuring. With so much sensitive information to safeguard and the need to secure unknown assets and devices, security leaders at Epiq knew that finding the right cybersecurity asset management solution was a priority.
Everybody thinks Axonius is a security tool, but my IT team loves the platform. They leverage it so often when we’re trying to manage a deployment or troubleshoot an IT issue. It’s the first place they turn every time.

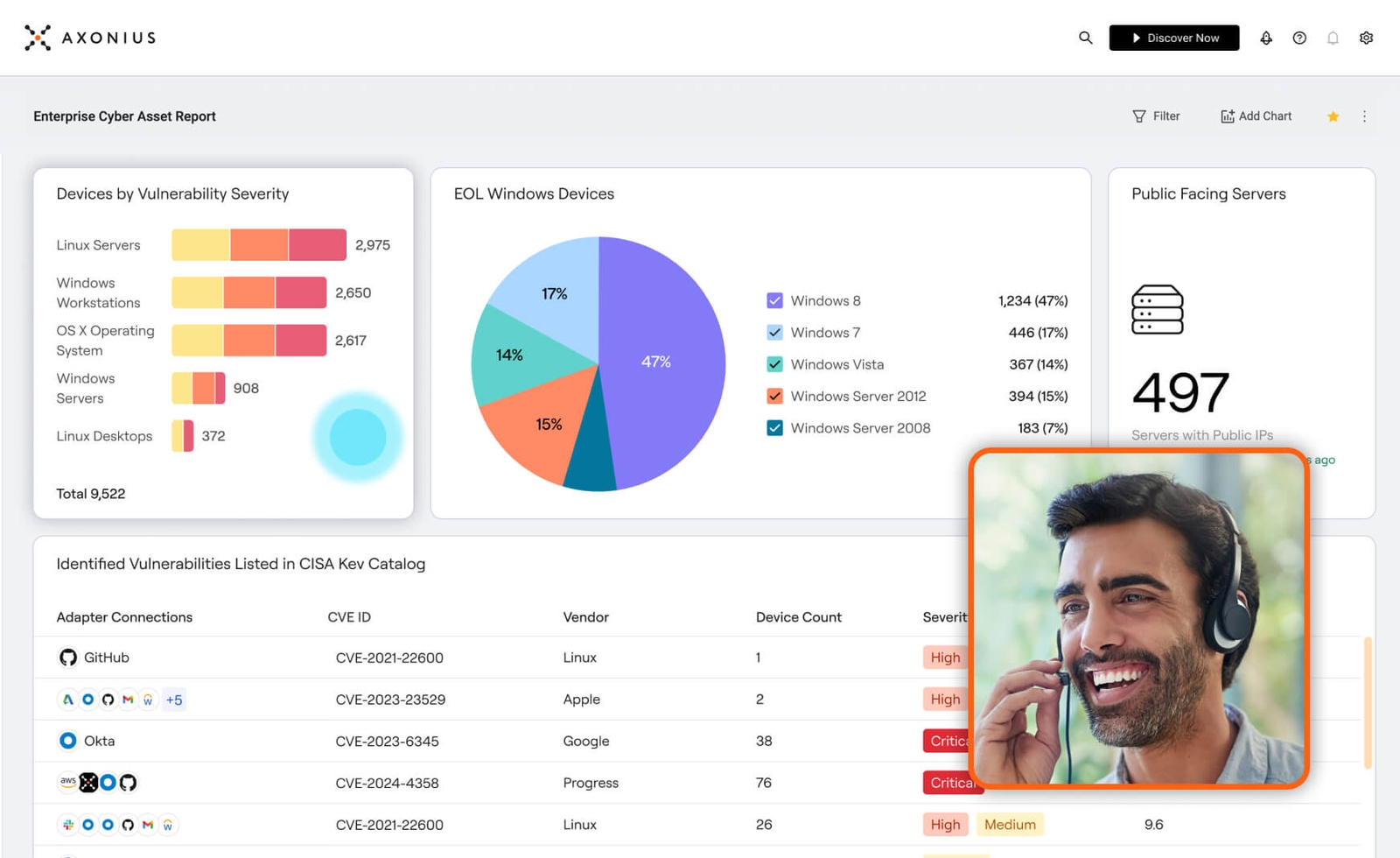
Before Axonius, asset management was a challenge. With so many individual systems across multiple on-prem and cloud environments, conglomerating all identities, workstations, and devices into one place seemed like an impossible task. That’s why Epiq chose Axonius as its asset management solution – to integrate these disparate sources of data into one single pane of glass that provides comprehensive visibility.
And from her perspective as incoming CISO, Alyssa Miller was glad asset management was made a priority. By the time she joined the team, Epiq was already deploying Axonius across the entire environment and was focused on maturity – and this made it much easier for Alyssa to continue building a robust cybersecurity program. She and her team now had a simple way to look through asset data, see where different technologies were deployed, and had a better understanding of their hybrid on-prem and cloud environments. Since then, Axonius has become an integral part of Epiq’s security program.
I honestly would recommend Axonius to any organization. It's such an easy tool to use. There's a lot of data management and discovery tools out there, especially in the cybersecurity space, but there are few that are as easy as Axonius.

The Swiss Army Knife of cybersecurity
At Epiq, Axonius isn’t only helpful for the security team. According to Alyssa Miller, “I joke with my peers that Axonius has become our Swiss Army Knife for different data discovery operations around our infrastructure. It’s become more than just a cybersecurity tool.” Axonius helps teams across Epiq identify deployment gaps, see where more controls are needed, and understand which assets aren’t fully covered. And if there’s an IT issue, Axonius is the first step for collecting data so teams gain a better understanding, can troubleshoot faster, and reach a resolution more quickly.
For example, Epiq was having an issue with certificate management. With Axonius, the team discovered key gaps that allowed them to revisit how they were managing certificates and be more proactive. To Miller, this is “a perfect example of how the strength of these integrations can be leveraged in ways that permeate through our entire environment and be a tool for every team across our organization.” Axonius is more than just a security tool – it’s an IT tool, an operations tool, a discovery tool, and a data management tool.
And without Axonius, there would be a lot more left on the team’s to-do list. Using the Microsoft Entra ID adapter allowed Epiq to not only discover assets that need connections, but to easily measure progress as well. It also highlights where legacy technology has created security gaps and what technology needs to be updated.
After gaining a better understanding of what needed to be modernized, Epiq recently migrated to the cloud. Leveraging Axonius during this shift provided greater visibility into how the environment is structured, showed exactly where technologies are deployed, and helped speed up the onboarding process for new partners – and these efficiencies are felt across the organization.
I didn't have to worry about some of those foundational elements of trying to build up an asset inventory or trying to visualize what across the environment was already in place. The Axonius connectors we utilized made it easier for me as an incoming CISO just to even understand the environment.

Delivering results
For Alyssa, the biggest benefit hasn’t just been the consolidation and efficiency that comes with using the product, but building a relationship with the Axonius team. “The team’s willingness to help us add certain capabilities, additional integrations, or even just minor features has really supported our growth and helped us use Axonius more effectively. From the start, Axonius has been a solid partner.” The Epiq team has found that implementation never seems to end – because they’re always growing and choosing to add more to their environments.
As we add technologies in other spaces, there are new integrations we can onboard to Axonius. And working with the people at Axonius makes these adoptions far more successful.

What really makes Axonius stand out for the Epiq team is that you’re not boxed into a specific set of solutions that integrate with the platform. “You can really customize it to fit whatever you need. Whether you’re a small team or a larger organization with a robust security program, Axonius can grow with you.”
Axonius has become an integral part of everything the Epiq security team does, according to Alyssa. Whether Axonius is automating remediation processes, discovering critical information about internal infrastructure, building efficiency, or compounding the capabilities of other systems, technologies and controls through adapters, Epiq plans on keeping this Swiss Army Knife in the toolbox.
When I think about Axonius and how important it is to our security program, words can't describe it. This tool is a key piece and an inherent element of everything we do. It drives our automation, discovery, and key portions of our strategy. Axonius provides the luxury of being able to evaluate where we stand by quickly visualizing our gaps as we build out our cybersecurity program.

Streamlining Epiq's security posture with AWS and Axonius
The Axonius and AWS partnership provides joint customers like Epiq with a more efficient approach to managing their ever-evolving cloud infrastructure and related security posture.
With the AWS and Axonius integration, customers can correlate AWS services, such as vulnerability findings from GuardDuty and security control insights from SecurityHub, with other IT and Security solutions to reduce their attack surface as they move more assets into the cloud. This integration delivers extended visibility and intelligence around security control coverage across AWS assets and provides deeper context to help customers understand whether AWS assets meet company policies and align with security best practices.
As an AWS partner, Axonius integrates with many AWS services, including Macie, SecurityHub, GuardDuty, and Inspector, to help customers mitigate threats, navigate risk, decrease incident response time, automate action, and inform business-level strategy.
Results
With Axonius, Epiq gained greater visibility into its environment, has a better understanding of where technologies are deployed, and increased efficiencies across the organization. Epiq now has a quick way to identify security gaps so they can be addressed immediately.
See Axonius in action
Discover what’s achievable with a product demo, or talk to an Axonius representative.




.png?width=950&auto=webp&format=jpg&disable=upscale)
