New research shows: In security, context is king — when it’s consistent
.png)
Most security teams have more visibility than ever. The opportunity now is making it usable – turning signals into contextual data that teams can trust and act on.
But context is also the hardest part to maintain. It doesn’t break inside tools; it breaks between them, where identity blurs, ownership drops, and impact has to be rebuilt.
That was one of the clearest patterns in our 2026 Axonius Actionability Report. In partnership with the Ponemon Institute, we surveyed 662 IT and security professionals in the United States to understand how security teams turn asset and exposure data into meaningful action.
Again and again, the answer came back to context. Our research surfaced three takeaways:
Context is fragmented across systems, so it isn’t applied consistently.
Context has a half-life, and most teams refresh it slower than environments change.
Decision-grade context needs engineering: consistent identity, clear ownership/criticality, and context that stays current.
Read our full report for more in-depth research and insights: Get the 2026 Axonius Actionability Report.
Context doesn’t usually disappear. It gets lost in translation.
Context should make the “so what?” clear without a scavenger hunt: What is this asset, how exposed is it, what’s connected, are controls holding or drifting?
Most organizations can answer pieces of that – in some systems. The progress is real. The problem is consistency. When context is scattered across inventories, security tools, cloud consoles, and ticket metadata, it becomes harder to standardize and apply consistently across workflows.
Our research quantifies that gap directly: only 23% of organizations say they always apply contextual data (asset criticality, exploitability, blast radius) to investigations. 27% say they never do. The rest fall somewhere in the middle, where context is available – just not consistently applied.
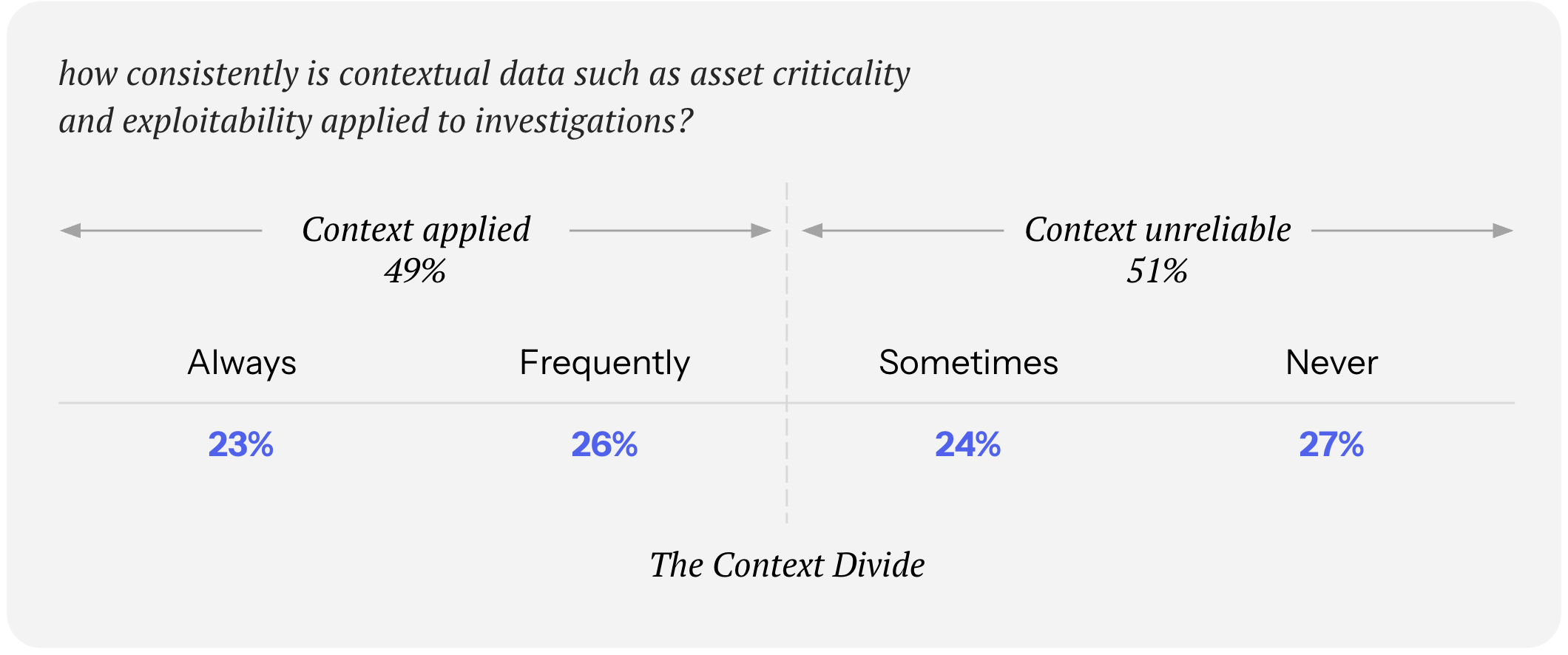
That’s the opportunity in practice: context exists. The win is making it durable and repeatable.
The three-headed bottleneck
We asked organizations to name their single biggest challenge in remediating exposures. The top answers were:
Unclear prioritization (26%)
No clear ownership (24%)
Inconsistent data across tools (21%)
_1.png)
Taken together, those aren’t three unrelated problems. They’re the same root issue – context that isn’t assembled and shared – showing up at different stages.
When the context is inconsistent, prioritization becomes a debate. When ownership isn’t attached, work gets rerouted or delayed. When data conflicts across tools, teams rely more on manual workarounds to reconcile what’s true.
Solve context once, and you remove friction everywhere it shows up.
Some things age like a fine wine. Context ages like milk.
Even when context is captured, it often expires faster than teams refresh it.
Our research found that only 30% reconcile asset inventories daily or monthly, meaning many environments are operating on context that’s already drifting by the time decisions are made. Meanwhile, 37% encounter asset data inconsistencies on that same cadence.
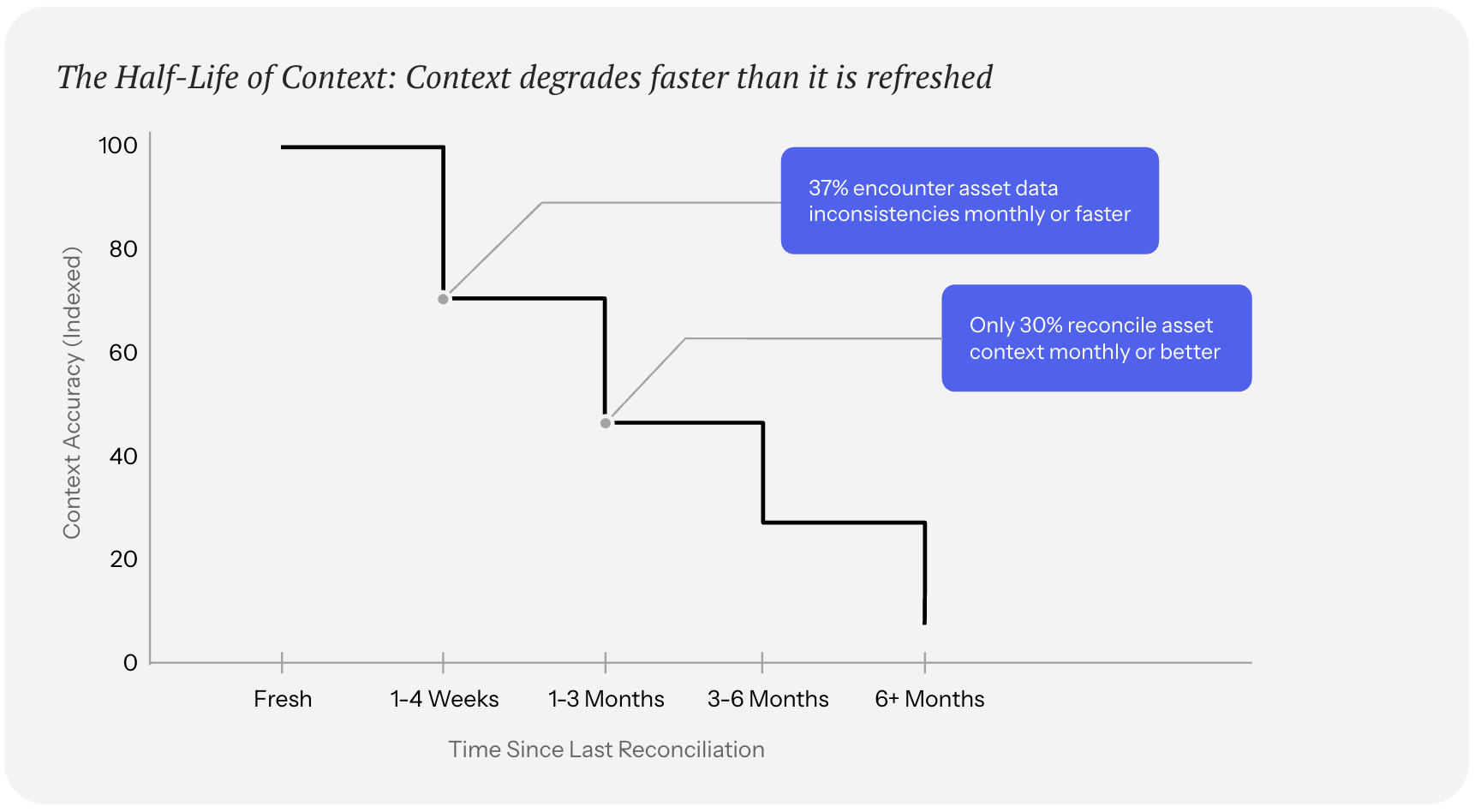
So the environment changes quickly, and the context layer changes slowly.
That mismatch creates predictable friction: assets get misidentified, ownership drifts, and confidence drops that the data reflects what’s actually live.
The result is a familiar pattern. Security teams can see plenty, but can’t reliably connect what they’re seeing to the right owners, the right dependencies, and the right business impact.
Fresh context is a force multiplier. It makes every handoff cleaner.
The Actionability Opportunity: Engineer the context layer
Our report’s findings point to a simple takeaway: actionability depends on truth, but truth is hard to come by when context lives in too many places.
But there’s a clear path forward. Engineer decision-grade context upstream – assembled and correlated before the work starts, and kept fresh as the environment changes.
Here’s what that looks like in practice:
1. Standardize profiles and relationships
If one system calls it a laptop, another an endpoint, and a third a hostname, you don’t have consistent context – you have aliases. Make profiles consistent so every downstream relationship holds.
2. Attach ownership and criticality where work happens
Ownership shouldn’t require a wild goose chase, and criticality shouldn’t live in a spreadsheet no one opens. Put both where decisions happen: findings, tickets, workflows.
3. Make freshness a design requirement
If your environment changes daily, stale context raises decision risk at scale. The cadence mismatch is the tell: refresh context at the pace the environment moves.
4. Keep the three context layers together
Decision-grade context has three layers that must travel together: security context, asset context, and business context.
The good news: most teams already have the raw data. The difference is correlation and consistency.
Get the 2026 Axonius Actionability Report
Here’s what our research makes clear: context breaks in the gaps between systems, it expires faster than most teams refresh it, and it has to be engineered – not rebuilt manually during every investigation.
That’s the Actionability Opportunity: build a context layer that’s assembled, correlated, and kept fresh, so the right details are already attached when an issue shows up.
Want the full dataset and the rest of the story? Read our 2026 Axonius Actionability Report.

Categories
- threats_vulnerabilities

Get Started
See how to make asset intelligence actionable with a guided demo:
- Stop chasing data — work from one asset model your entire team can trust.
- See what's exposed before it's a problem — surface coverage gaps automatically.
- Turn alert noise into action — cut thousands of alerts down, to the ones that matter.
