Your asset inventory ends at IT. Your risk doesn’t.

Julissa Caraballo
Principal Product Marketing Manager, Axonius

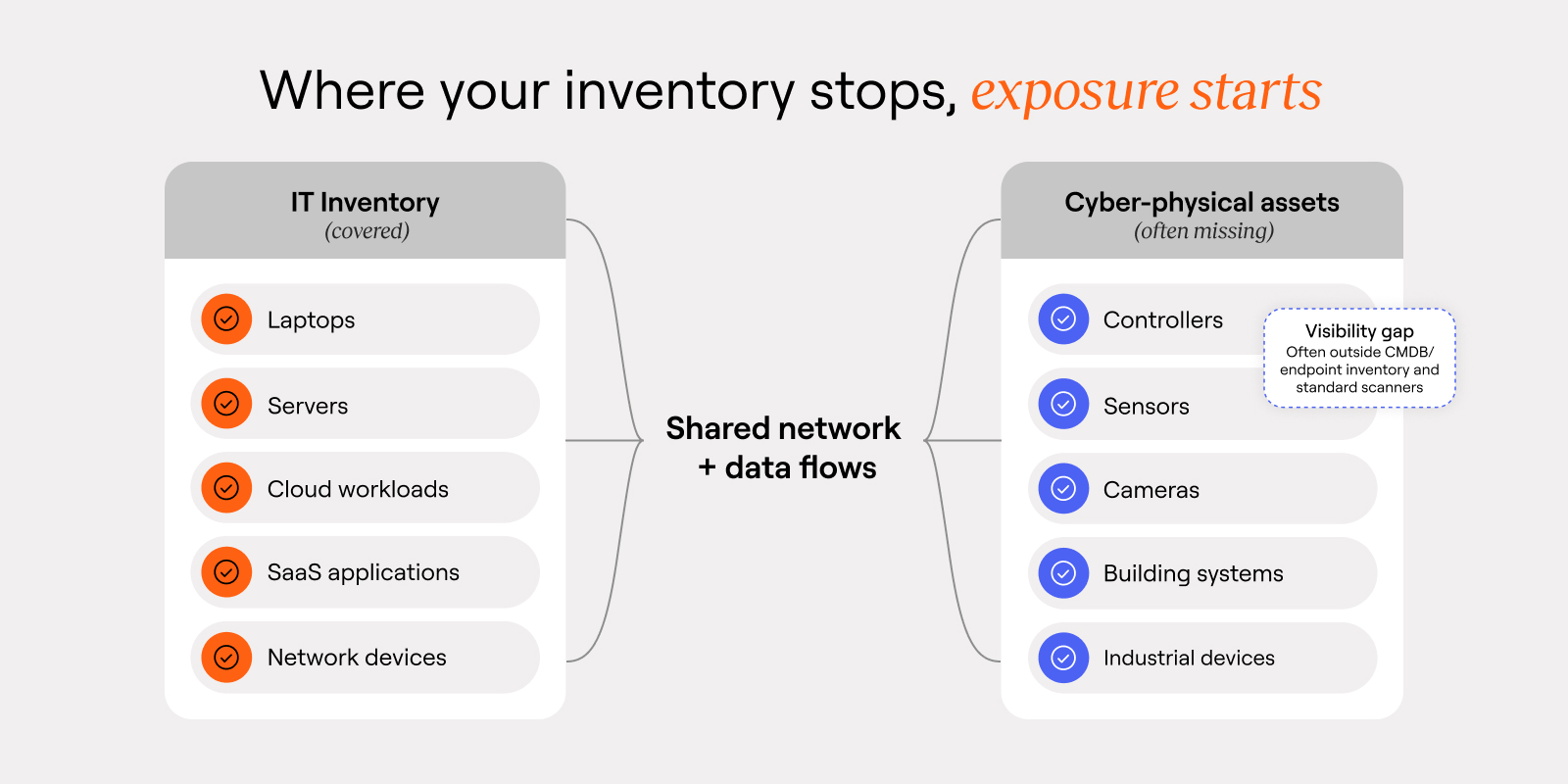
You probably have a clean count of laptops, servers, and cloud workloads.
Now the harder question: what else is on the network?
Controllers. Sensors. Cameras. Building systems. Industrial devices.
Most organizations can’t answer that because their asset inventory stops where IT stops. But the exposure doesn’t. When you lack OT asset visibility, entire categories of risk go unmanaged.
Smart buildings, connected factories, clinical environments, and vendor-managed infrastructure run alongside business-critical applications. They share networks and data. Yet they also slip past the tools security teams use to track assets and respond.
When those systems don’t show up in your inventory, they don’t show up in your risk models, your segmentation plans, or your incident response playbooks either.
So when an IT incident spills into physical systems, teams are already behind. The real risk doesn’t start when attackers move laterally. It starts when you never knew what was there in the first place.
When IT OT convergence creates new security gaps
IT and operational systems used to be treated as separate domains. That line is gone.
Operational environments depend on enterprise networks and cloud services. Manufacturing relies on digital platforms for scheduling and monitoring. Buildings depend on centralized systems for access control, HVAC, and energy management. Campuses and critical infrastructure run on software-driven control layers.
As IT OT convergence accelerates, the security implications grow. A vulnerability in a management system, a misconfigured network segment, or a compromised identity can translate into real disruption.
Not because attackers suddenly care about PLCs or cameras, but because they care about the easiest path to business impact. And cyber-physical environments give them options when you can’t see what’s connected or prove what’s segmented.
If you can’t see these assets, you can’t answer the questions that define exposure:
What’s connected to production networks?
What sits outside endpoint and identity controls?
What expands the blast radius during an incident?
Without those answers, teams manage exposure based on assumptions instead of evidence.
Compliance now demands proof
Regulators are moving past paperwork. They want evidence that controls hold up in the real environment.
Across industries, frameworks and mandates increasingly require organizations to demonstrate four things:
Complete asset inventories
Segmentation between operational and enterprise networks
Continuous monitoring of vulnerabilities and access paths
Evidence that controls are actually working
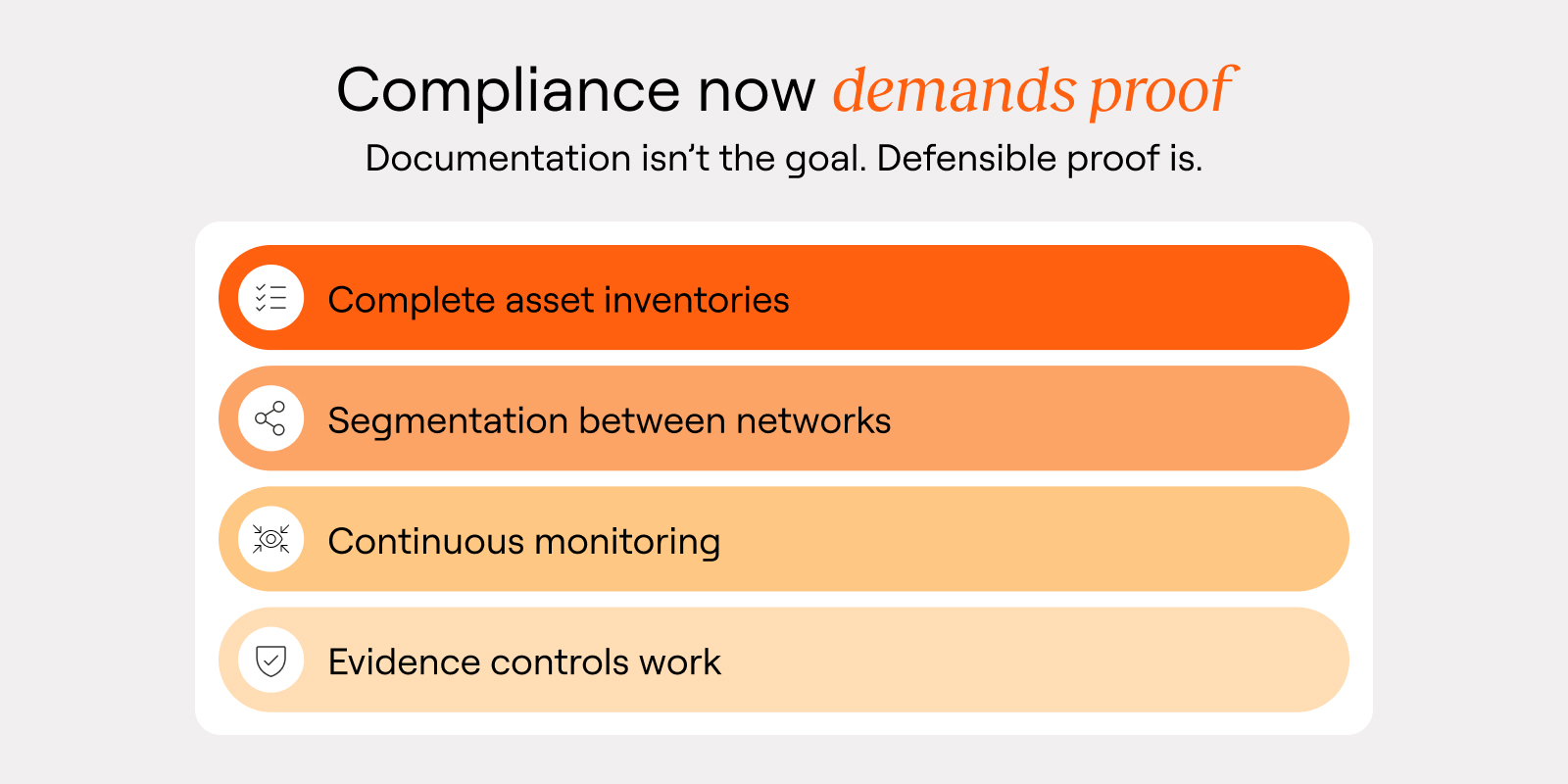
In many cyber-physical environments, the source of truth is still fragmented: spreadsheets, maintenance platforms, vendor records, and network diagrams that drift out of date.
Audits turn into a scramble. Teams spend weeks reconciling device lists, validating ownership, and explaining why certain systems fall outside standard security tooling. Even when they pass, many don’t trust the result. Reports look clean, but no one feels confident about the actual posture.
More importantly, compliance gaps often mirror resilience gaps.
If an incident hits, and you can’t quickly identify which devices are affected, what operations they support, and how they connect to the rest of the environment, recovery slows down. Outages last longer. Risk increases. Leadership starts asking why security couldn’t see the impact sooner.
Resilience is more than prevention. It’s knowing what matters, what’s connected, and what breaks first when something goes wrong.
Why IT tools miss OT and cyber-physical assets
Many organizations try to extend IT tooling into operational environments. It rarely works.
Cyber-physical systems come with constraints that break traditional approaches:
Devices can’t run agents
Active scanning may disrupt sensitive equipment
Vendor systems may sit outside corporate management platforms
Non-standard protocols can limit compatibility with IT tooling
The result is familiar: OT asset blind spots across large portions of the environment that remain invisible to endpoint tools, cloud security platforms, and even vulnerability scanners. And even when devices are detected, they often lack context: Who owns them? What do they support? What’s the operational impact if they go offline?
Without that context, remediation stalls and segmentation stays untested. You don’t get an execution plan. You get a list.
The move to unified asset intelligence
The shift underway isn’t a new category of devices. It’s a new operating model for how organizations think about assets and risk.
Instead of siloed inventories, leading teams build unified asset intelligence that correlates devices, networks, applications, identities, vulnerabilities, and operational dependencies.
_-_1600x800px.jpg)
That puts cyber-physical systems into the same workflows security already runs: exposure management, incident response, compliance validation, and segmentation strategy.
It also changes what teams can answer with confidence:
Which vulnerabilities matter based on real exposure paths?
Which operational systems amplify blast radius?
Which assets require coordination across IT, OT, and facilities teams?
That’s what security maturity looks like in a connected environment: one risk model, one operating picture, and fewer blind spots.
OT asset visibility starts with seeing the full picture
Asset management used to focus on what was easy to inventory: laptops, servers, cloud workloads.
But the systems that drive revenue, safety, and customer experience extend beyond IT. Buildings, factories, campuses, and infrastructure are connected, software-driven, and exposed to the same threat paths, with higher stakes when things fail.
This isn’t IT hygiene. It’s business risk.
If you manage cyber and physical environments in separate visibility silos, you’ll keep relearning the same lesson during audits and incidents. If you unify asset intelligence across both, you can understand exposure in context and act with confidence.
Risk doesn’t stop at the firewall. Visibility can’t either.
Categories
- endpoint_and_iot_security

Get Started
See how to make asset intelligence actionable with a guided demo:
- Stop chasing data — work from one asset model your entire team can trust.
- See what's exposed before it's a problem — surface coverage gaps automatically.
- Turn alert noise into action — cut thousands of alerts down, to the ones that matter.
