We asked 600+ security pros how they prioritize exposures. There's more than just CVSS.

Most security teams already know what exposure prioritization should look like. Exploitability, blast radius, business impact; the inputs are well understood. The challenge is making it operational.
When context isn't reliably available at decision time, even the best prioritization intent defaults to the nearest available input. For most organizations, this is still severity.
That was one of the clearest patterns in our 2026 Axonius Actionability Report. In partnership with the Ponemon Institute, we surveyed 662 IT and security professionals in the United States to understand how teams turn asset and exposure data into meaningful action.
In our first article in this series, we explored why context breaks between systems. This piece picks up where we left off: what happens when that broken context meets the prioritization engine.
Our research surfaced three takeaways:
Severity still dominates prioritization by default. Not because teams prefer it, but because the infrastructure for context-driven prioritization isn't there yet.
The intent-to-execution gap is structural, not cultural. Teams want context-driven prioritization but can't apply it consistently.
Closing the gap is an engineering problem. Assemble the context layer upstream, not during every triage cycle.
Read our full report for more in-depth research and insights: Get the 2026 Axonius Actionability Report.
Severity scores: The comfort food of exposure prioritization
CVSS was designed to describe technical severity, and it does that well. But it was never designed to be a prioritization engine, and that’s how most organizations use it.
Our research found that 56% of organizations still rely primarily on blunt scoring systems like CVSS to drive prioritization. That's more than half the market leaning on a system that can't distinguish between a critical CVE on an internet-facing production database and the same one on an air-gapped test box nobody's touched in six months.
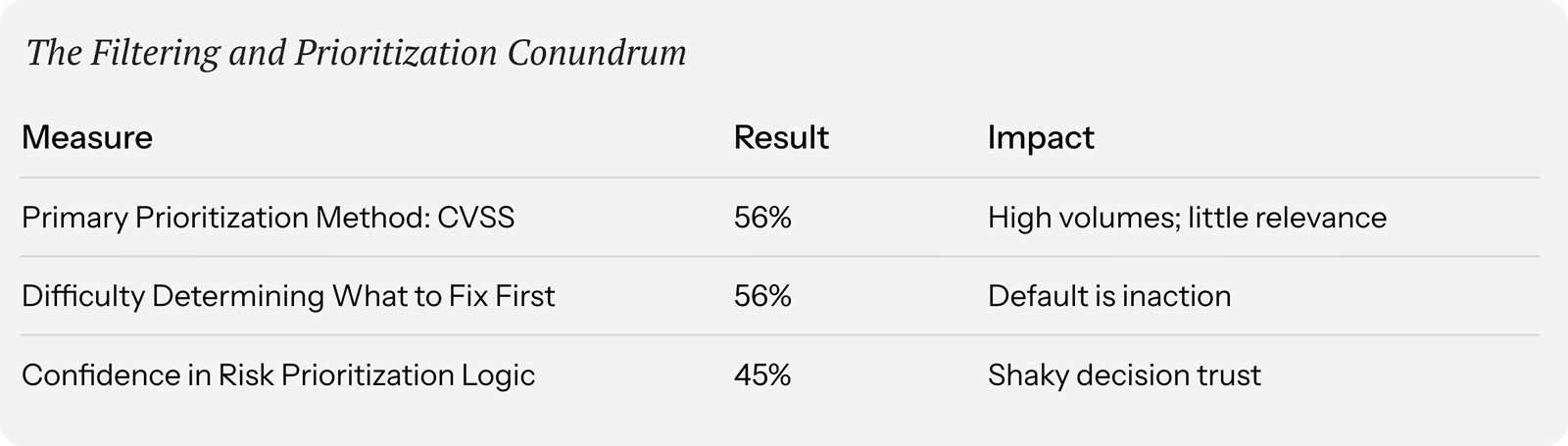
Severity is absolute. Risk is relative. A CVSS 10.0 is a 10.0 regardless of where it lives, who owns it, or whether there's an active exploit in the wild. But risk depends on all of those things. So when 56% of organizations also say they have difficulty determining what to fix first, it's not surprising. When your primary filter strips away the context you need to decide, the queue doesn't get prioritized. It just gets long.
When everything is critical, nothing is. And when severity is the only input, everything looks critical.
Good intentions, leaky pipes
Organizations largely agree on what context matters for effective prioritization: exploitability, blast radius, and business impact. But wanting context and having it reliably available at decision time are two very different things.
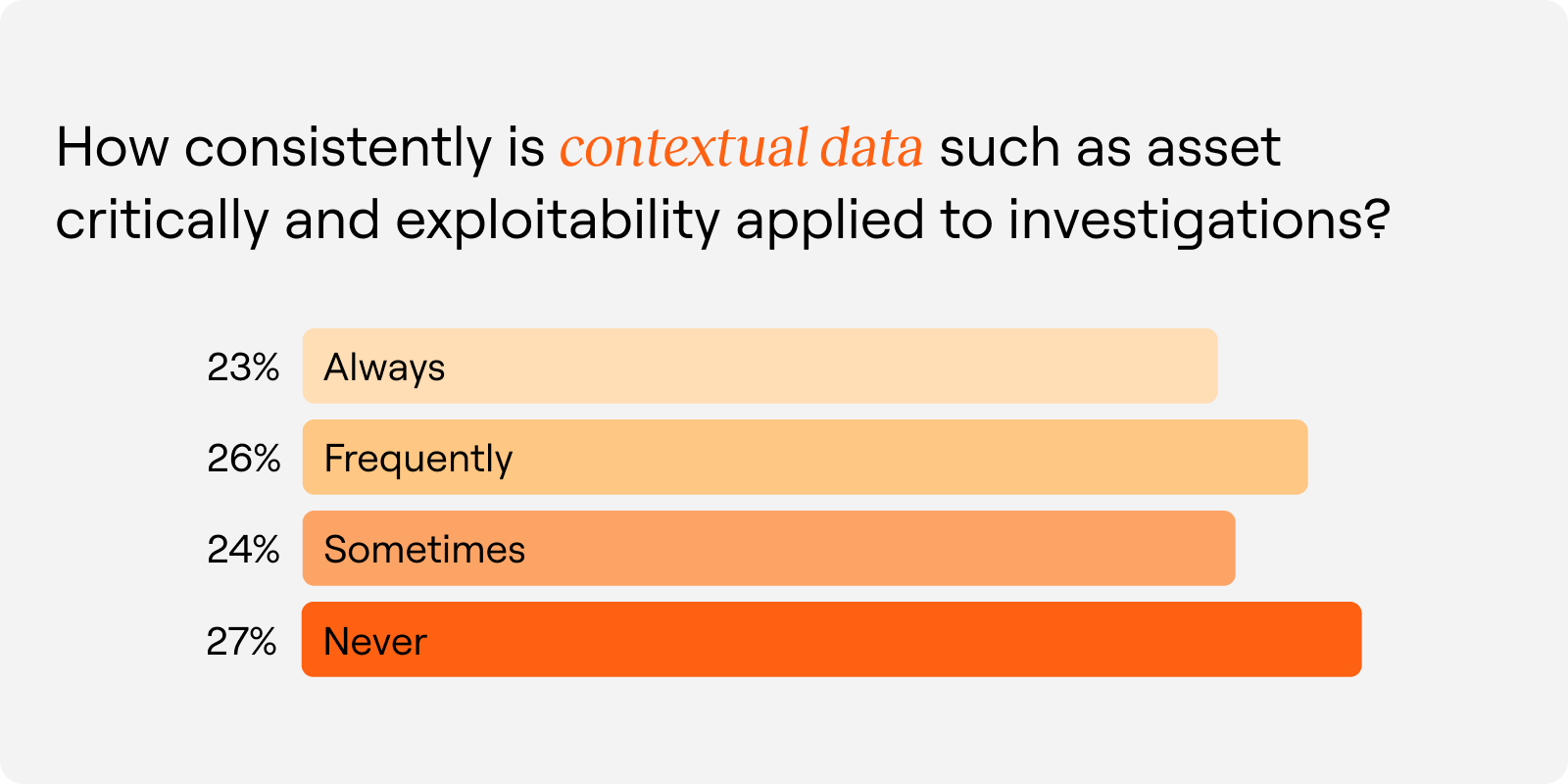
Only 23% of organizations always apply contextual data to investigations, and 27% never do. The rest fall somewhere in between, where context shows up when someone has time to track it down and disappears when they don’t.
That in-between is where the real story lives. These aren’t teams that have given up on context-driven prioritization. They’re teams where the context layer is too fragmented, manual, or stale to apply consistently. The intent is sound, but the infrastructure to support it isn’t.
A scavenger hunt that nobody signed up for
Here’s the pattern we see play out again and again: a finding surfaces, a ticket gets created, and the scramble starts. Who owns this asset? What environment is it in? Does it touch regulated data? Is the EDR agent even running?
The answers exist—scattered across consoles, a CMDB that was last reconciled during the previous audit cycle, and a spreadsheet no one maintains consistently. 51% of respondents said they miss needed context during remediation, not because the data doesn't exist, but because it isn't assembled at the speed decisions need to happen
This is why severity wins by default; it's the one input that's always there. The CVSS score shows up automatically, while the context that would turn that severity call into a risk call requires manual assembly that changes with every finding.
No wonder only 45% of organizations express confidence in their risk prioritization logic. The rest are pushing work downstream on a foundation they're not fully sure of.
The Actionability Opportunity: From severity-driven to context-driven prioritization
The path from severity-driven to context-driven prioritization is about removing the structural barriers that force smart teams into blunt decisions.
That means engineering the context layer: building systems where security, asset, and business context are assembled and correlated before a finding ever lands in a queue.
Here’s what that looks like in practice:
1. Layer the three contexts together
Effective exposure prioritization requires security context (severity, exploitability, active threats), asset context (what is this, where does it sit, who owns it), and business context (what data does it touch, what breaks if it goes down). When those three travel together, prioritization becomes deliberate.
2. Assemble context upstream, not during triage
If the first step in every investigation is a scavenger hunt across four consoles, you've already lost the consistency battle. Context needs to be attached before findings hit the queue.
3. Keep context fresh
Only 30% of teams reconcile asset inventories daily or monthly, while 37% encounter data inconsistencies on that same cadence. Prioritization decisions are only as good as the recency of the inputs behind them.
4. Make the output actionable, not just accurate
A prioritized list that doesn't include ownership, routing, or remediation guidance is just a smarter queue that stalls at the first handoff.
Get the 2026 Axonius Actionability Report
The severity-to-risk gap is an infrastructure problem. The organizations closing it are the ones treating context as something you engineer, not something you reconstruct manually every time a finding shows up.
That’s the Actionability Opportunity: build the context layer so that context-driven prioritization is the default.
Want the full dataset and the rest of the story? Read our 2026 Axonius Actionability Report.
_1.png)
Categories
- Threats Vulnerabilities

Get Started
See how to make asset intelligence actionable with a guided demo:
- Stop chasing data — work from one asset model your entire team can trust.
- See what's exposed before it's a problem — surface coverage gaps automatically.
- Turn alert noise into action — cut thousands of alerts down, to the ones that matter.
