The business case for asset intelligence: real numbers from real deployments

Security teams already know they have an asset problem.
The spreadsheet is out of date the moment it's saved. The CMDB was built for ticketing, not security decisions. The vulnerability scanner missed something last quarter and the auditor flagged it.
Asset intelligence solves a problem every security team already knows it has. The harder question is whether it produces enough value to justify the investment. The data shows it does.
To explain this, we’ll walk through the three operational pains we hear most from customers, why the status quo keeps failing to solve them, and the quantified outcomes of adopting asset intelligence, built off dozens of customer interviews, investigative reports from leading analysts, and hundreds of deep-dives conducted annually with our users.
3 problems that show up in every cybersecurity environment
Across the customers we speak with every day, the same three operational problems surface again and again, regardless of industry or stack maturity.
1. Asset inventory data no one trusts. Security teams plan, prioritize, and report against asset inventories that everyone already knows are incomplete. The spreadsheet is stale, the CMDB is missing critical context, and the EDR console only knows about the assets it's installed on. Every downstream process inherits this gap. When the answer to "how many assets do we have?" is a different number depending on who you ask, the answers to "are we covered?" and "what's our exposure?" become a best guess.
2. Security control gaps you can't see until it's too late. Many organizations have between 10% and 25% of their assets missing at least one required security control. EDR isn't installed. The vulnerability scanner doesn't know about it. The asset is running an old OS that's out of compliance. The team only finds out when an auditor flags it, an incident exposes it, or a question from leadership forces someone to go count manually. The gap was always there; visibility into the gap was the missing piece.
3. Vulnerability response slowed by manual correlation. Scanners produce thousands of findings a week. The team triages instead of fixing. Critical vulnerabilities sit open past SLA because nobody has a fast way to answer "which of these matter to us, on which assets, owned by whom, and what's the blast radius?" The work is slow because the data lives in five different tools and the correlation is manual.
Without asset intelligence, these problems compound. Untrustworthy asset data leaves coverage gaps invisible, which drags out vulnerability response, which means the next audit or incident starts the whole cycle over.
Why spreadsheets and CMDBs can’t solve the asset problem
Spreadsheets fail at scale and freshness. Cloud instances spin up and down, employees onboard and offboard, devices move physical locations, and the spreadsheet can’t reflect any of it without manual updates. By the time the team has reconciled the spreadsheet against the EDR console, the network scanner, and the cloud provider, the underlying environment has already changed.
CMDBs were built for ITSM, not security. They exist to support change management, ticketing, and service mapping. It's a system of record for what IT thinks should be in the environment, not a real-time picture of what actually is. Most CMDBs are populated by manual entry or by integrations that run on a schedule slow enough to miss the assets that matter most.
The "buy more tools" approach makes it worse. Each new tool adds its own partial view of the environment and its own integration burden. The team ends up with more data, less correlation, and a higher operational cost. The data sources exist. What’s missing is an asset intelligence layer that consolidates, deduplicates, and correlates them into a single trustworthy picture.
What does the ROI of asset intelligence look like?
The Forrester Total Economic Impact study, commissioned by Axonius, quantified what an asset intelligence platform produces across a composite organization. The value lands in three categories, and the customer stories below show what these outcomes look like in practice:
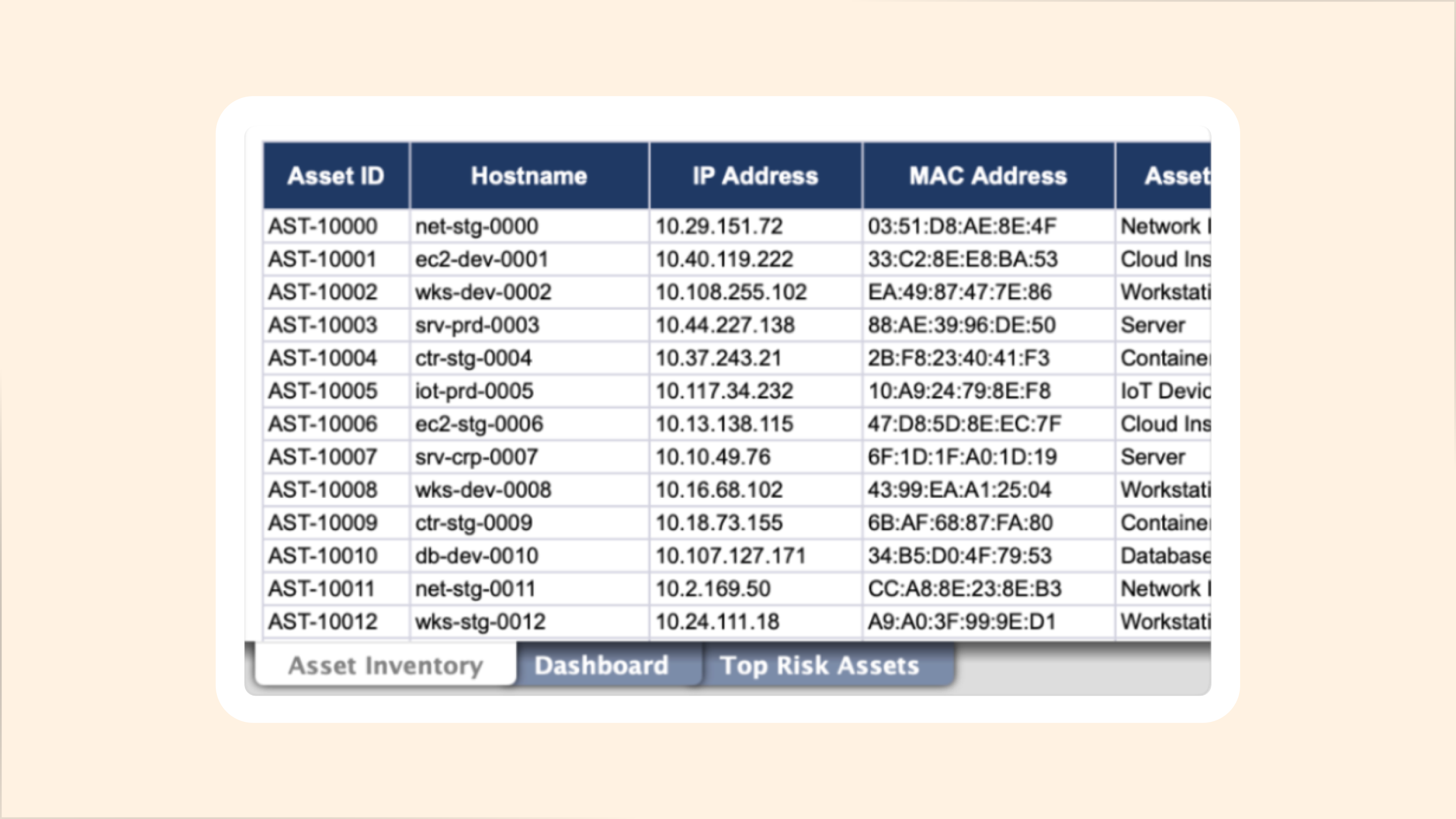
ROI of asset intelligence | Forrester finding | Customer result |
Cost savings | 60% reduction in time maintaining asset inventories (~625 hrs/yr recovered) | Biotech company cut SaaS license spend by 50% |
Risk reduction | 150% more assets identified than pre-Axonius inventory | Lumen Technologies reduced overall risk by 40% after infrastructure migration |
Productivity gains | 70% faster vulnerability investigation and prioritization; 90% savings on other vuln mgmt activities | InComm Payments reduced months of manual asset tracking to minutes |
Cost savings: Recovered hours and rationalized spend
The Axonius asset intelligence platform displaces hours of manual work across asset inventory maintenance, audit preparation, and data reconciliation. It also surfaces opportunities for license rationalization, since organizations frequently discover they're overpaying for tools that are deployed inconsistently across their environment.
Forrester found a 60% reduction in time spent maintaining accurate asset inventories for the Axonius customer. For a team that previously spent twenty cumulative hours a week on inventory upkeep, that's roughly 625 hours a year recovered, or a third of an FTE redirected to higher-value work.
Epiq, a global legal services company, used Axonius to eliminate manual work that slows security teams down at every turn. From zero-day response to audit prep, the team stopped spending hours tracking down asset context, chasing ownership, and reconciling competing inventories, and started getting answers from a single place.
"With Axonius correlating infrastructure, software, and organizational data into a single view, security teams can now move directly from detection to decision to action, without wasting critical hours chasing the right owner." — Alyssa Miller, CISO, Epiq |
TransUnion, a consumer credit reporting company, used Axonius to automate the ownership and compliance work that was quietly consuming engineering time across the organization. Remediation workflows that used to start with tracking down the right person now route automatically, and endpoint agent compliance runs on daily monitoring instead of manual review.
"A huge amount of time was wasted just figuring out who to talk to…now remediation can actually start immediately." — Kara Keene, Senior Manager of Attack Surface Reduction, TransUnion |
In another instance, a fast-growing biotech company reduced license spend by 50% on one of its major SaaS applications because Axonius surfaced insights into actual usage patterns the team didn't have before.
Risk reduction: Gaps found, gaps closed
The second category is harder to quantify in dollars but easier to quantify operationally. Customers who deploy Axonius consistently report that they discover assets they didn't know about, find coverage gaps they didn't know existed, and close exposures that were previously invisible.
Forrester's TEI found that Axonius customers identified 150% more assets than their pre-Axonius inventory suggested. This reflects the real gap between what teams thought was in their environment and what was actually there. Every one of those previously unknown assets was operating outside the security stack until it became visible.
Lumen Technologies, a global telecommunications company, used Axonius to turn a fragmented view of millions of devices into a risk-based system leadership could actually act on. What started as an inventory problem became the foundation for every risk decision that followed, from zero-day response to board-level reporting
"The visibility Axonius was able to shed on the end-of-life issues we had with our systems directly contributed to the decision to migrate the majority of our infrastructure to the cloud, reducing overall risk by 40%." — Geoff Krahn, Director of Product and Platform Security, Lumen Technologies |
Khaleeji Bank, a financial services firm in Bahrain, used Axonius to get ahead of regulatory requirements and close the visibility gaps that made accurate risk assessment impossible. With a unified view of their environment, the security team stopped depending on other departments to tell them what was exposed and started making that call themselves.
"By leveraging this powerful solution, we have achieved a level of autonomy and control that is unparalleled. Our newfound empowerment has allowed us to establish an incredibly resilient security framework, free from external dependencies." — Yusaf Hasan Husain, Information Security Manager, Khaleeji Bank |
Productivity gains: Faster teams, not bigger ones
The third category is the one that security leaders care about most in operational reviews, not because it means fewer people, but because it means the team you already have can operate at the scale the environment actually demands. Axonius lets the team move faster across the workflows where speed matters: vulnerability response, incident investigation, audit preparation, and cross-functional coordination with IT.
Forrester found 70% time savings in investigating and prioritizing impacted assets during vulnerability response, and 90% time savings across other vulnerability management activities. Those numbers translate directly into faster remediation cycles and tighter SLA hit rates.
InComm Payments, a global financial technology company, used Axonius to accelerate project work across security, IT, and operations. Teams that previously spent months tracking down asset data, chasing compliance gaps, and coordinating across departments could get answers in minutes and move on to the next problem.
“Overall, it’s increased our workflow by 30%, which says a lot about having this type of tool…it’s literally at our fingertips, which has been completely amazing. Axonius has enabled us to move faster and complete more tasks at a better pace.” — Tiffanie Joseph, Former Technical Security Program Manager, InComm Payments |
Lionbridge, a global translation services company, used Axonius to replace a patchwork of disconnected systems with a single view of their entire asset inventory. Security and IT teams stopped arguing about whose data was right and started actually solving the problems underneath.
"Axonius provides us with a single source of visibility and a single source of truth. We're no longer arguing about what's there and what's not.” — Doug Graham, Chief Trust Officer, Lionbridge |
A global specialty retailer used Axonius to turn a full-team, multi-day scramble into a one-person, few-minutes task. When an incident hit, the security engineer stopped dropping everything and started answering the question from the console before the meeting was over.
"It takes minutes (not days) by one person (not the whole team) to get the information we need. Interestingly enough, Axonius also helps us quickly get to the bottom of almost every other asset-related question that we can dream up." — Staff Senior Security Engineer, Global Specialty Retailer |
Asset intelligence raises the return on every other security investment
The composite Axonius customer in the Forrester TEI study realized a meaningful three-year ROI driven by labor savings, reduced incident impact, faster audit cycles, and tool consolidation. The customer references above are individual examples of where those numbers come from in practice. Each customer's specific outcome will be different, but the categories of value are consistent.
Axonius isn't a nice-to-have visibility layer. It's the foundation that makes every other security investment more effective, and every decision made based on it more accurate.
EDR works better when you know which assets are missing it. Vulnerability management works faster when you know which assets a CVE actually applies to. Compliance audits go more smoothly when the asset evidence is already correlated. The platform pays for itself by making the rest of the security program produce more value per dollar spent.
The three pains above are the ones we solve, the customer references are the ones we publish, and the numbers are the ones a third party validated. The question of whether Axonius produces enough value to justify the investment has an answer. It's in this post.
Build your own business case for asset intelligence
If you're evaluating how to improve your asset intelligence practice and want to put numbers against your own environment, a business value assessment with the Axonius team gets you a defensible model that is unique to you.
Set up time with an expert and learn how Axonius helps security teams close coverage gaps, reduce exposure, and stay ahead of risk: request a business value assessment.
Sources: Forrester Total Economic Impact study commissioned by Axonius, March 2025. Customer stories published at axonius.com/customer-stories. Quotes drawn from customer interviews and published case studies; some have been condensed for length.
Categories
- Asset Management

Get Started
See how to make asset intelligence actionable with a guided demo:
- Stop chasing data — work from one asset model your entire team can trust.
- See what's exposed before it's a problem — surface coverage gaps automatically.
- Turn alert noise into action — cut thousands of alerts down, to the ones that matter.
