CISA BOD 26-02 overview: How Axonius empowers you to meet compliance

Allison Judge
Inside Sales Engineer, AFS

Rachel Lucas
Senior Sales Engineer - Federal Civilian, AFS

Tim Boyd
Senior Sales Engineer, AFS

Dave Klein
Federal Systems Integrator Sales Engineer, AFS
.png)
End-of-support (EOS) edge devices are among the weakest links in your organization’s cybersecurity posture. That’s why the Cybersecurity and Infrastructure Security Agency (CISA) issued Binding Operational Directive (BOD) 26-02. This latest BOD raises the alarm and directs action on still-active edge devices that lack vendor support.
That’s right: those legacy routers, firewalls, VPN gateways, load balancers, and other externally-facing assets that once protected and ran your network but no longer receive security updates have become high-value targets for threat actors.
Nation-state adversaries are actively exploiting these devices, which places your organization at risk. In fact, we routinely see edge devices that have been forgotten (deployed but not documented or not actively managed), miscategorized, or assumed retired but are still active and exposed. Recent trends indicate these are the exact devices hackers target first.
To combat and manage this risk, CISA requires you to perform the following actions and report compliance via CISA-provided templates:
Immediately: Identify and update EOS software — including firmware — on edge devices
Within 3 months: Identify all devices on the CISA EOS Edge Device List
Within 12 months: Upgrade or decommission all devices on the CISA EOS Edge Device List and identify those that will become EOS within the succeeding 12 months
Within 18 months: Upgrade or decommission ALL EOS edge devices, including those not on the CISA EOS Edge Device List
Let’s take a closer look at what BOD 26-02 means for your agency and how the Axonius Asset Cloud helps you accomplish each of these requirements.
Identify and update EOS software
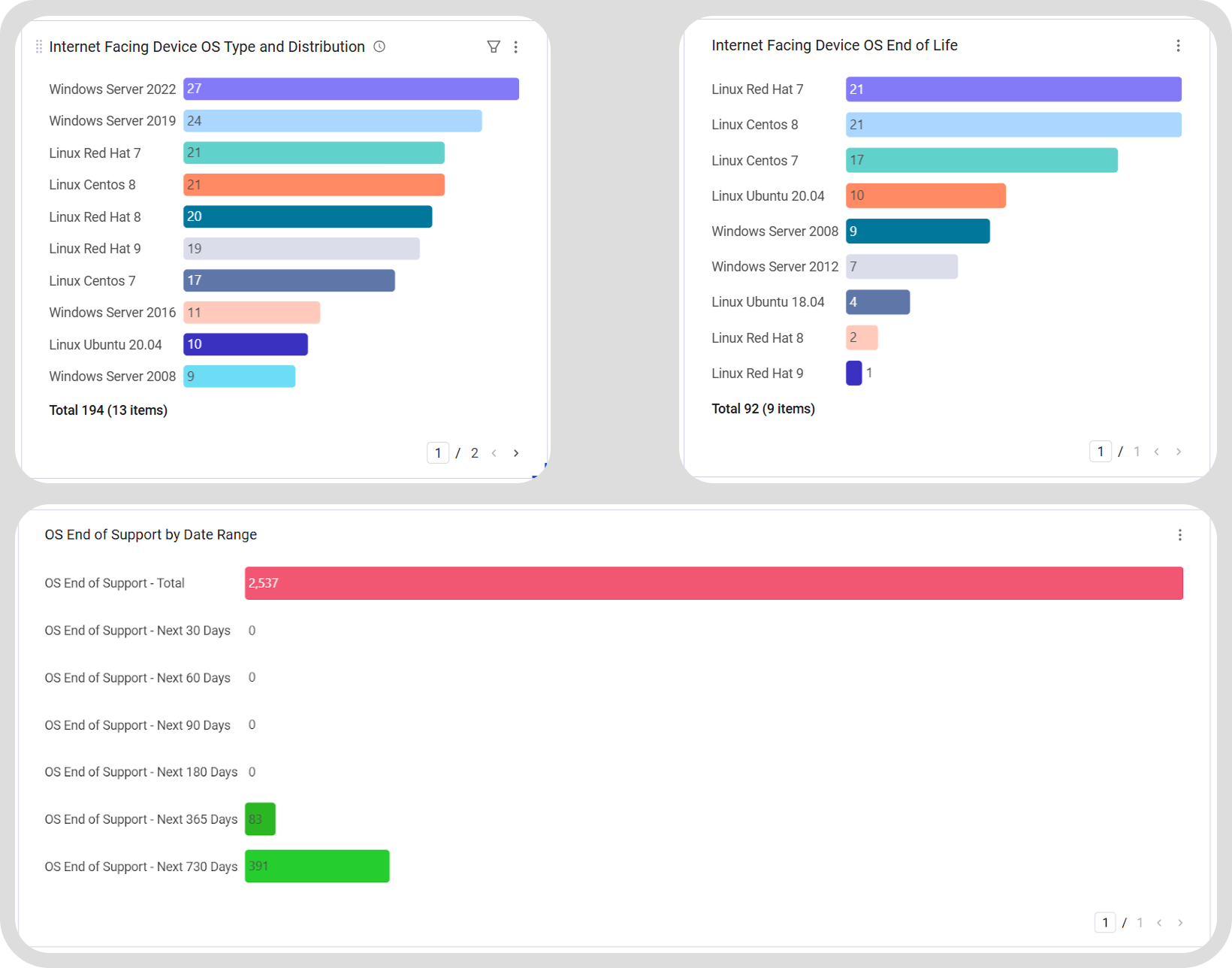
BOD 26-02 is not limited to hardware alone. In many cases, supported edge devices may still be running outdated operating systems, firmware, or other software that is end-of-life (EOL) or EOS. These software components can introduce the same level of risk as unsupported hardware.
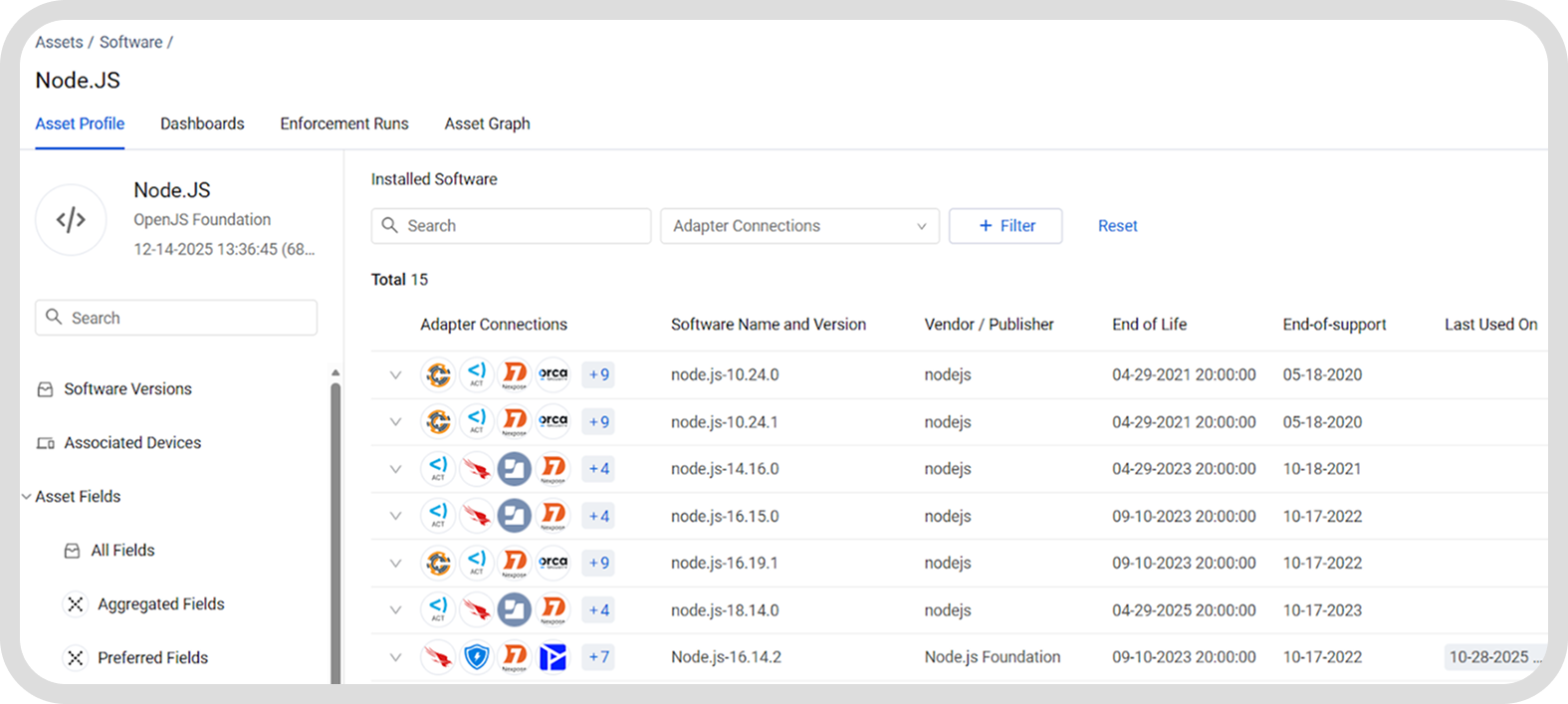
That’s where Axonius Software Assets comes in. Software is one of more than 40 asset types that the platform correlates with. With the ability to query software based on a subset of devices, Axonius is uniquely positioned to enable rapid identification of EOL/EOS software on edge devices.
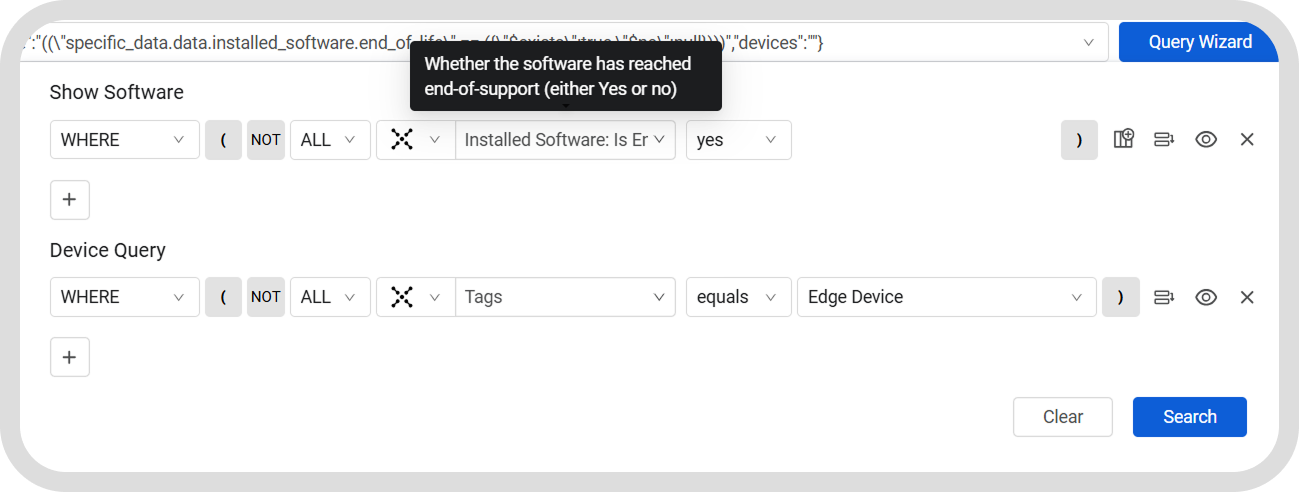
The built-in Axonius Catalog provides software lifecycle intelligence by documenting EOL/EOS dates for software assets. This enables you to easily identify software that is no longer supported or reaching EOS, even if the underlying device hardware remains supported.
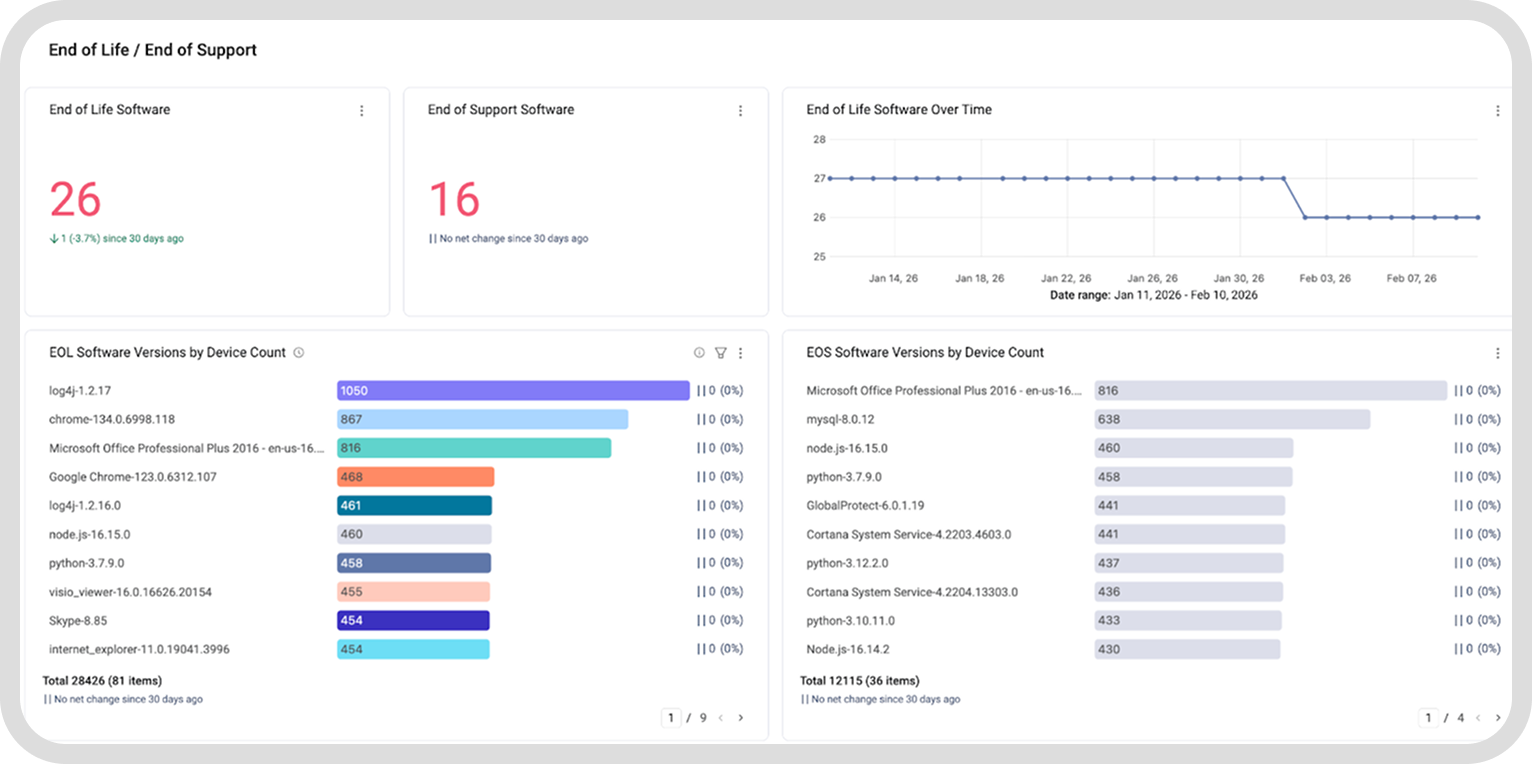
Additionally, the Software Registry allows you to designate software approvals based on agency-specific software policies. You can input EOS dates for specific software versions, label them as “Not Approved,” and enforce policy accordingly. This complements the Axonius Catalog metadata and allows you to easily detect new installs of EOS software.
_1.png)
Upgrade or decommission EOS edge devices
BOD 26-02 requires you to identify all devices in the CISA EOS Edge Device List and report that information to CISA within the required timelines. This applies to devices that are currently EOS as well as those that will reach EOS within the next year.
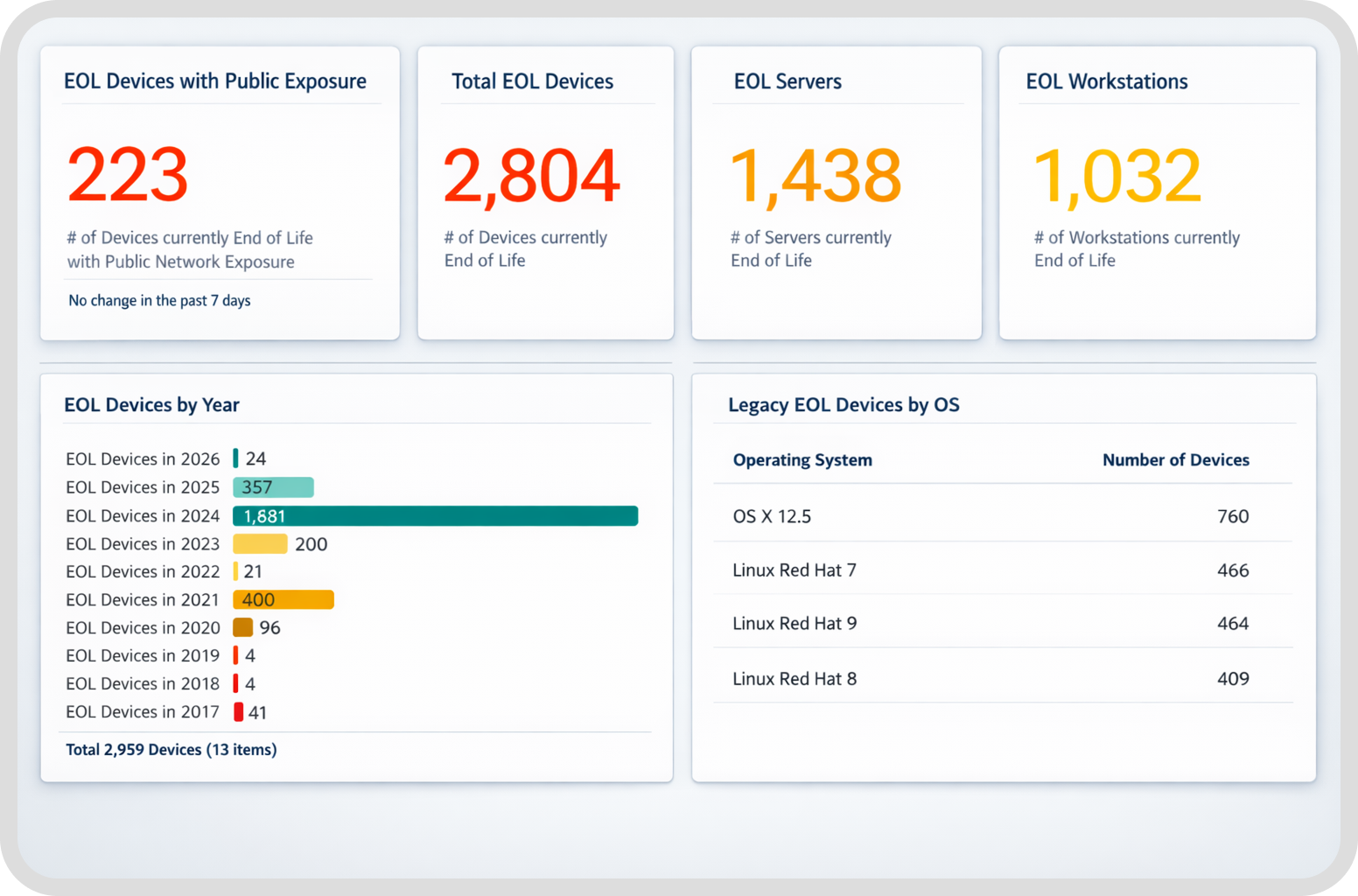
Like most BODs, this one requires you to have full visibility of your operational environment. While this seems like a straightforward task, many organizations are forced to utilize manual inventory processes due to not having a single authoritative source of cyber asset data. We often hear from federal teams that edge devices are managed by different groups, were deployed years ago, or were never fully documented to begin with. These issues make EOS tracking especially difficult.
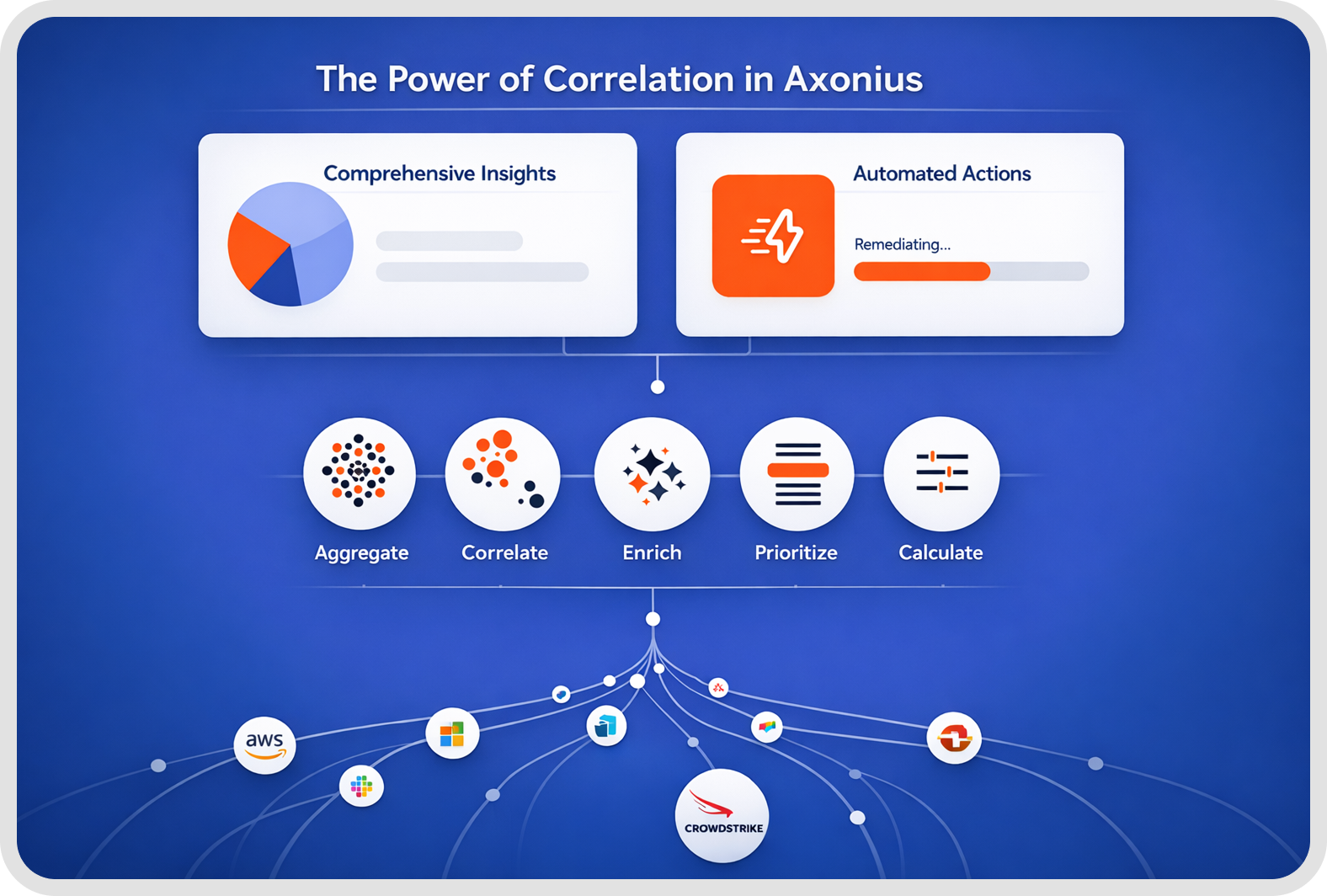
Axonius is purpose-built to easily identify and flag edge devices with its extensive Adapter Library and built-in enhancements that, together, provide comprehensive asset visibility and context. You gain visibility into manufacturer and model, hardware version, installed software and firmware, deployment location and exposure, and device ownership and usage.
This context gives you the ability to filter edge devices that are relevant to the directive. You’ll establish an authoritative source of truth so your team can rapidly identify EOS or near-EOS edge devices and expedite compliance.
However, that’s just the beginning. Next, you must either update supported hardware running EOS software or remove EOS devices entirely from your network. This is where many teams encounter challenges. Even after EOS devices have been identified, coordinating updates, replacements, or compensating controls can be slow and complex tasks.
Axonius provides actionable intelligence that allows you to quickly target EOS devices that must be updated or removed. The Axonius Action Center enables remediation workflows as soon as defined conditions are met, such as a device reaching EOS or presenting elevated risk. These actions can include creating upgrade or replacement tickets, isolating or restricting device access, and preventing unsupported devices from re-entering production.
CISA’s Edge Device List also calls out vulnerabilities applicable to those devices. Axonius has the National Vulnerabilities Database (NVD) built into the platform and integrates CISA’s Known Exploited Vulnerabilities (KEV) catalog through the Exposures module. You can continuously map KEVs to discovered assets and directly correlate them with EOS edge devices to prioritize what’s actively being targeted.
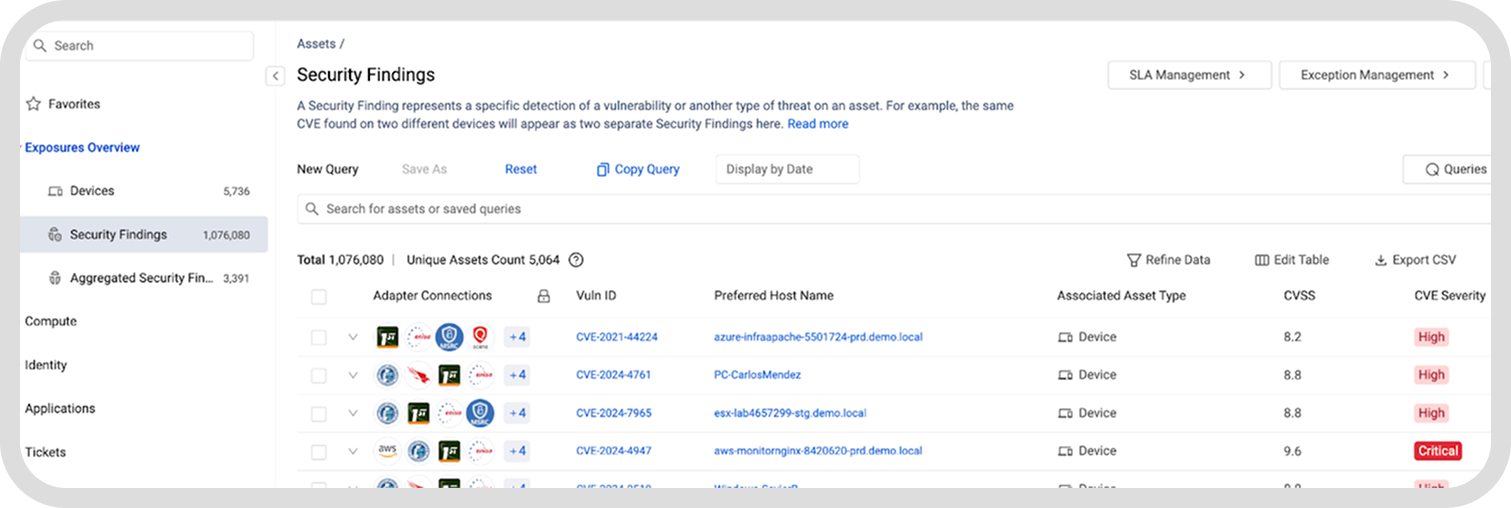
Moreover, one of the more than 500 out-of-the-box automations in the Axonius Action Center is a Custom Risk Score feature. Customers can decide which asset data points, including EOS devices and EOS software, contribute to risk and assign a weight (percentage) to each factor. The result is a quantitative “Axonius Risk Score” that can be leveraged to monitor, prioritize, and enforce agency-defined risky assets.
Continuously find and monitor edge devices
BOD 26-02, like BOD 23-01 and Zero Trust strategies, is not a one-time exercise. Compliance depends on your ability to continually discover edge devices, monitor their status, and prevent new risks from emerging over time. One of the biggest lessons from prior BODs is that point-in-time inventories are almost immediately outdated. Without continuous discovery, agencies end up seeing and reporting what happened at a previous date and time, rather than current data.
To mitigate this issue, BOD 26-02 requires you to proactively manage edge devices across their entire lifecycle, from deployment through retirement. Axonius makes lifecycle management part of your continuously orchestrated security operations.
With historical reporting, you can monitor devices in your Axonius inventory throughout their lifespan, continuously track vendor support status and firmware age, and prevent EOS devices from being onboarded into production in the first place. You can also audit lifecycle posture across your entire agency.
Axonius correlates disparate data from multiple sources into a single authoritative asset inventory and maintains a historical record of physical, virtual, and cloud-based edge devices. You always know which devices exist now, how they are deployed, what risk they present, and how this information has changed over time, meeting CISA’s mandate for continuous visibility while proactively reducing exposure.
It’s also worth noting that many of the requirements outlined in BOD 26-02 align directly with capabilities agencies have already deployed as part of their Continuous Diagnostics and Mitigation (CDM) program. Axonius has been selected as a system of record to feed Federal Civilian CDM data pipelines. Because Axonius can leverage existing CDM investments to support BOD 26-02 compliance without introducing new tooling or parallel processes, it is the cornerstone to meeting both mandates.
By leveraging Cyber Asset Management, Axonius Software Assets, and Axonius Exposures, you’re positioning your agency to support long-term CDM sustainment, expanded module adoption, and broader security modernization efforts while also satisfying BOD 26-02 requirements.
The bottom line: Eliminate blind spots, minimize attack surface, reduce risk
BOD 26-02 requires you to report accurate and current information on EOS edge devices to CISA and demonstrate progress against required timelines. Manual reporting, however, often relies on spreadsheets and fragmented data sources, making it difficult to produce complete and defensible reports.
Axonius streamlines reporting by serving as an authoritative source of truth for edge device inventory and EOS status. Because asset data is continuously refreshed, normalized, and deduplicated, you can automatically generate accurate reports and answer data calls in a way that reflects the current state of your environment and trends over time, rather than via stale, outdated snapshots.
With historical reporting features, you can maintain auditable records of discovery, remediation, and enforcement activities. This allows you to demonstrate sustained compliance over time and show clear alignment with CISA’s mandate to continuously identify, track, and refresh all edge devices.
BOD 26-02 makes proactively identifying and addressing unsupported EOS edge devices a top priority, but meeting this objective without total visibility and automated processes is unrealistic. As threat actors continue to actively exploit exposed, unpatched cyber assets and software at the network edge, you must eliminate blind spots and minimize your attack surface — not only to satisfy BOD 26-02, but to reduce real and ongoing risk to your agency’s mission.
Axonius core features and enhancements, including Cyber Asset Management, Exposure Management, Software Assets, Action Center, and historical reporting, create the ideal platform to comply with the directive.
Have questions about BOD 26-02 compliance? Let us show you how Axonius can help.
Categories
- Compliance And Frameworks
- Federal

Get Started
See how to make asset intelligence actionable with a guided demo:
- Stop chasing data — work from one asset model your entire team can trust.
- See what's exposed before it's a problem — surface coverage gaps automatically.
- Turn alert noise into action — cut thousands of alerts down, to the ones that matter.
