600+ security pros exposed the real vulnerability remediation bottleneck — and it's not a tools problem

Security teams have a hard enough time working through what to fix first, but the even harder part is getting the fix across the finish line. An exposure can be correctly identified, accurately prioritized, and fully contextualized, and still stop cold the moment it needs to become someone's job.
That's the core challenge of exposure remediation, and it's what separates risk remediation in theory from risk remediation in practice.
In our 2026 Axonius Actionability Report in partnership with the Ponemon Institute, we surveyed 662 IT and security professionals to understand how teams turn asset and exposure data into meaningful action — not just for traditional vulnerability remediation, but across the full spectrum of exposures.
In earlier pieces from this research, we explored why security context breaks between systems and why exposure prioritization still defaults to severity. This piece picks up where both converge: remediation.
Our research surfaced three takeaways:
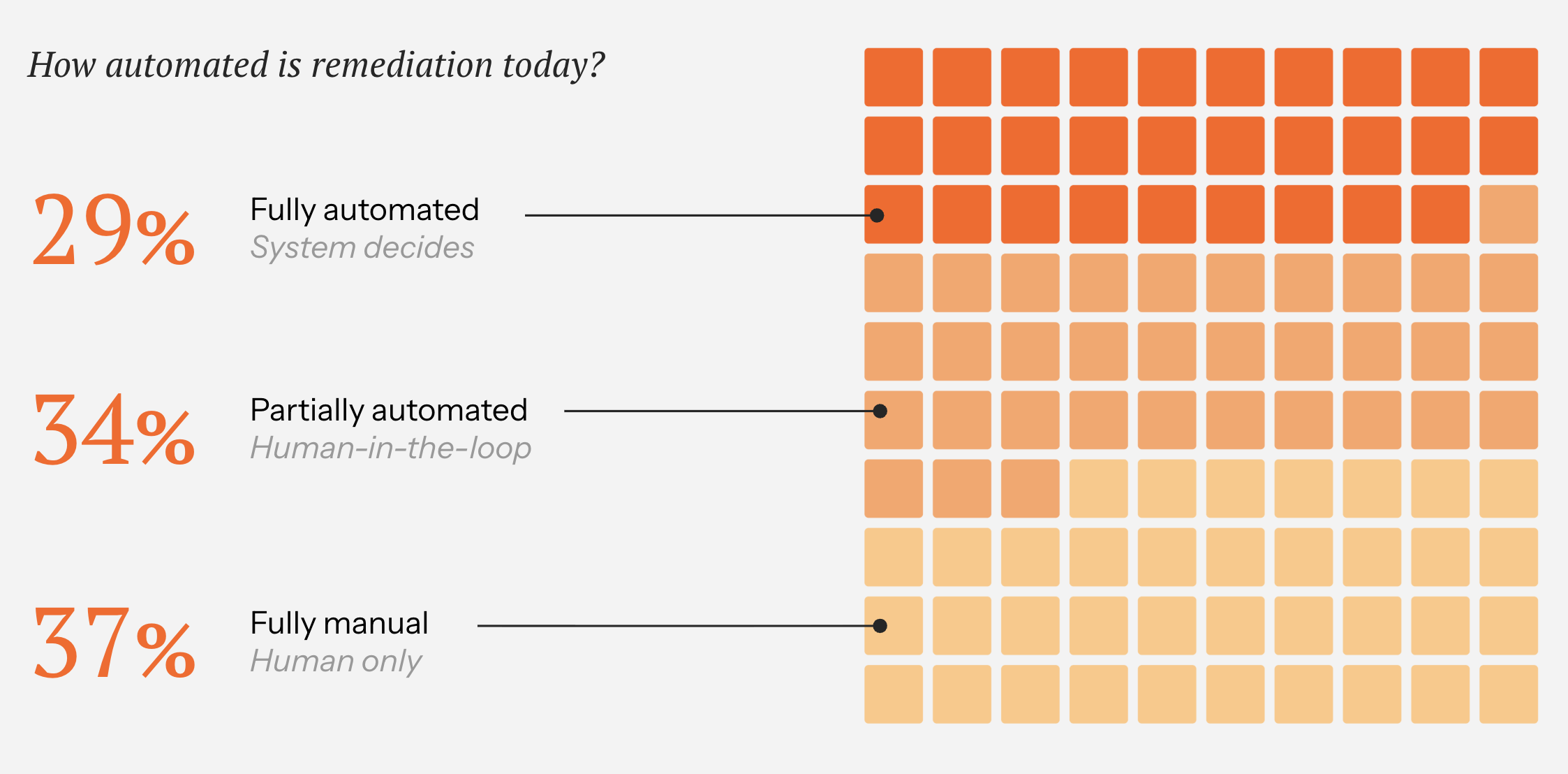
Remediation is still largely manual, and the teams doing it know it isn’t working. More than a third run fully manual workflows, and 55% rate themselves ineffective at completing prioritized exposures on time.
Ownership is the silent stall point. Security remediation breaks down when nobody owns the fix. Only about half of organizations assign an owner when a new exposure is identified, and the rest are routing work through systems that don’t agree on who’s responsible.
AI shows promise but isn’t ready to lead. 52% of organizations are willing to act on AI-driven recommendations, but 63% say those recommendations lack the context they need.
Read our full report for more in-depth research and insights: Get the 2026 Axonius Actionability Report.
The duct tape holding exposure remediation together
Here’s the uncomfortable math: 37% of organizations still run fully manual remediation workflows. Another 34% are partially automated with a human in the loop. Only 29% have reached full automation, and even that number comes with caveats about scope and confidence.
Meanwhile, 55% of respondents still track remediation progress in spreadsheets. Not as a backup. As the system.
The consequence is predictable: 55% rate themselves ineffective at completing prioritized exposures in a timely manner. Mean time to remediate (MTTR) suffers because the coordination layer between decision and action is manual. The truth is, the operational layer between “this needs to be fixed” and “this got fixed” is held together with manual effort that doesn’t scale.
Return to sender: When nobody owns the remediation fix
An exposure can survive perfect triage and still die in the handoff. Only 51% of organizations assign ownership when a new exposure is identified. As for the other half, the finding lands with no name on the envelope.
Even among organizations that do assign ownership, the plumbing is fragile. The most common method — automatic routing based on tags and metadata (37%) — depends on tagging consistency that only 32% of organizations maintain. While the intent is right, the infrastructure just isn’t there yet.
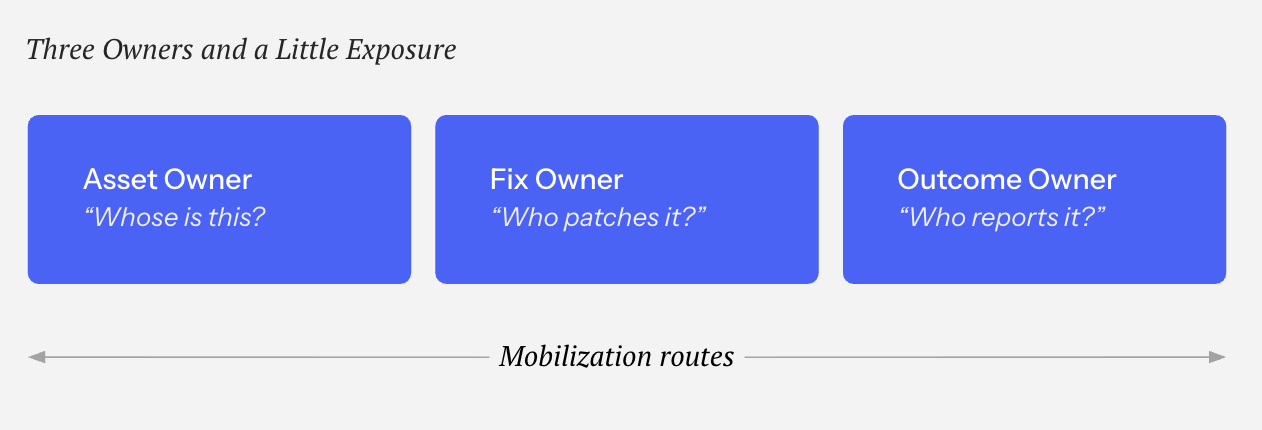
Yet, owning an asset isn’t the same as owning the fix, and owning the fix isn’t the same as owning the outcome. In practice, these responsibilities route across different teams through different systems: 37% of remediation flows automatically based on metadata, 24% gets assigned to IT or security, 20% requires manual investigation, and 19% routes to the impacted business unit.
AI wants the job, but the resume needs work
The appetite for automation is real. 52% of organizations say they’re willing to execute automated actions based on AI-driven recommendations. That’s a meaningful signal of trust, and a clear indicator of where teams want to go.
But willingness without infrastructure creates its own risks. 63% say AI recommendations lack important information, and only 35% have safeguards in place to prevent automation from going off the rails. In that context, it’s less surprising that spreadsheets are still the coordination backbone for more than half of organizations.
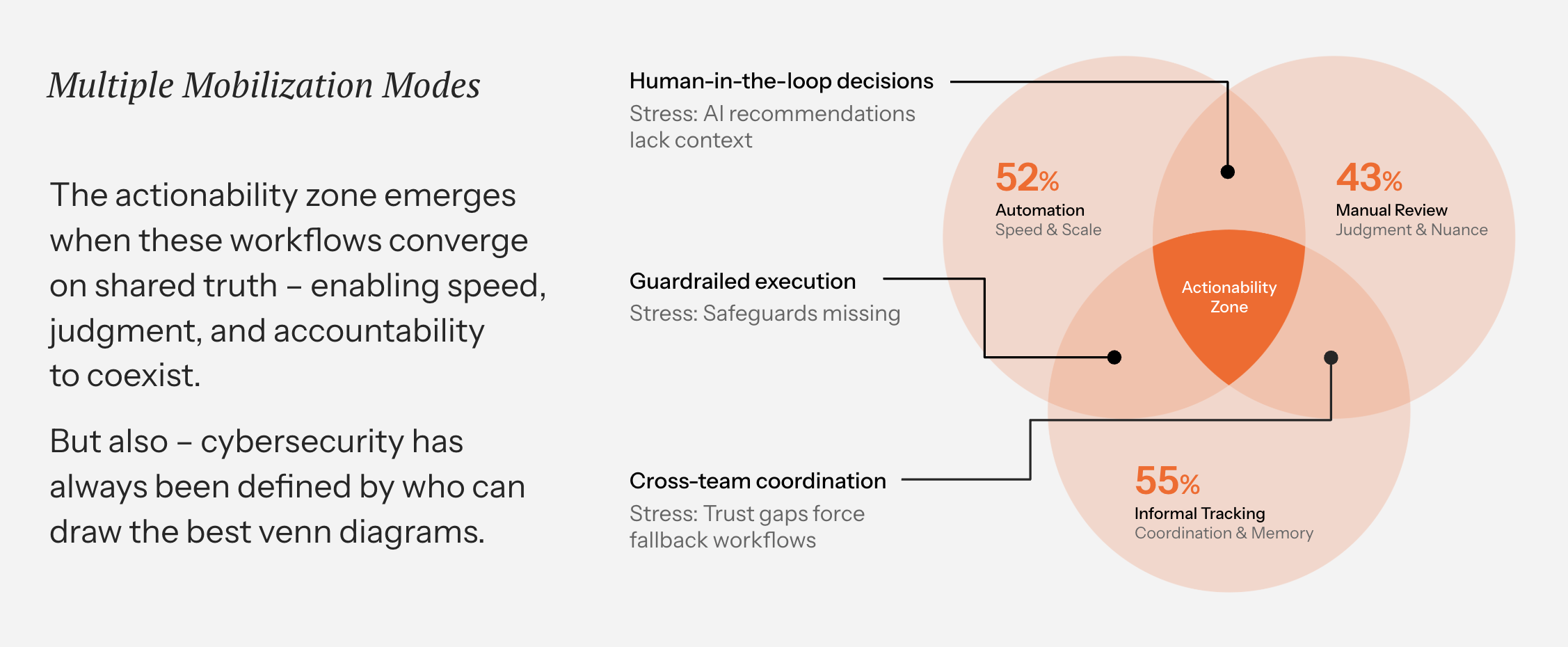
Automation scales what's already working — it doesn't fix what's broken. If the context layer is fragmented, ownership is unclear, and workflows are manual, automatic remediation on top of that simply creates faster mistakes.
The organizations getting this right are building the foundation first: trusted data, clear ownership, repeatable workflows. Then, they let automation accelerate what already holds.
The Actionability Opportunity: Coordinate remediation without conformity
Cybersecurity remediation needs a shared foundation. Different mobilization modes — automated enforcement, human-in-the-loop decisions, cross-team coordination — will always coexist. The problem is when those modes operate on different data.
Here’s what grounding them in the same truth looks like:
1. Make ownership explicit across the lifecycle
Asset owner, fix owner, outcome owner — these are different roles that route through different systems. When ownership is attached to the asset and travels with the finding, the “who owns this?” question stops blocking the fix.
2. Replace the spreadsheet layer with coordinated workflows
Spreadsheets become the system of record when nothing else connects the dots. Tracked tickets, SLA-driven workflows, and remediation actions that route through the tools teams already use eliminate the manual reconciliation tax.
3. Automate what’s earned it, not everything at once
Start with repeatable, low-risk actions: closing known coverage gaps, enforcing policies on well-understood asset types, and routing tickets with verified ownership. Build automation trust incrementally, not aspirationally.
4. Ground every action in decision-grade data
Automated, manual, or hybrid: different mobilization modes only conflict when the underlying data does. When every workflow starts from the same reconciled view of assets, exposures, and ownership, coordination holds even as methods vary.
Get the 2026 Axonius Actionability Report
Remediation stalls when the operational layer between decisions and fixes is fragmented. That’s the Actionability Opportunity: anchor every action to a shared source of truth so that coordination holds, ownership is clear, and fixes land where they’re supposed to, regardless of how they get there.
Want the full dataset and the rest of the story? Read our 2026 Axonius Actionability Report.
.png)
Categories
- threats_vulnerabilities

Get Started
See how to make asset intelligence actionable with a guided demo:
- Stop chasing data — work from one asset model your entire team can trust.
- See what's exposed before it's a problem — surface coverage gaps automatically.
- Turn alert noise into action — cut thousands of alerts down, to the ones that matter.
