Actionability: The next frontier rooted in fundamentals

Dean Sysman
Co-Founder and Executive Chair
.png)
Seven years ago, I was sitting on a plane at JFK, watching a snowstorm cancel my flight to San Francisco for RSAC. Axonius had been selected as one of ten finalists for the RSAC Innovation Sandbox that year. This opportunity gave us three minutes on stage to pitch cybersecurity asset management to a panel of judges and a packed room. Our CMO ended up presenting in my place, and we won. The judges said something that stuck with me: they were impressed that a problem as "unsexy" and "mundane" as asset management could produce the most innovative startup of the year.
That was 2019. We had a thesis that knowing what you have is the first step to securing your environment. Since then, we’ve evolved the meaning of cybersecurity asset management to asset intelligence, and have been driving the evolution of visibility to actionability. What has held true since then is that “unsexy” space is the load-bearing wall for every major cybersecurity program: security operations, incident response, exposure management, risk & compliance, and cyber resilience. You can't prioritize what you can't see, and you can't fix what you can't trust.
Now AI has raised the stakes again. Agents are spinning up identities at breakneck speed. Agentic workflows are making decisions autonomously. Shadow AI is proliferating faster than shadow IT ever did. Every one of these trends depends on the same foundational question we pitched in 2019 – what do you have, how is it configured, who owns it, and what is its state?
This year, I was fortunate to be back at RSAC without any flight mishaps, taking the main stage for a keynote presentation. What a long way to come in seven years.
The perfect cybersecurity world
It would have been easy to stand up there and raise alarms about AI. But I wanted my keynote to be positive and encouraging, so instead I started by painting a picture of the perfect cybersecurity world: self-healing environments.
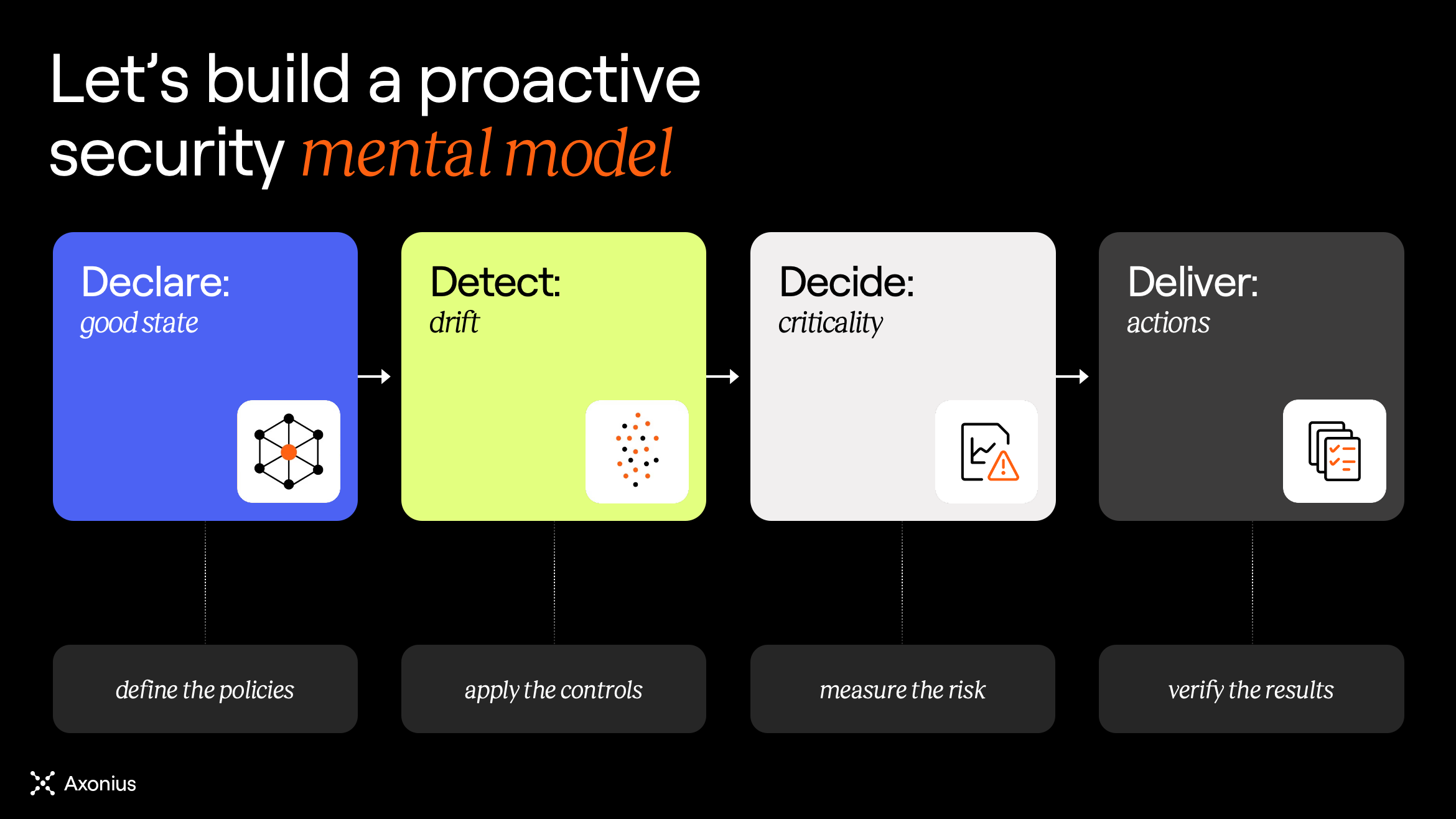
There’s a simple mental model to follow here: declare what you want to be true across the environment, detect deviations from that truth, decide if the deviation matters, and deliver actions to restore the truth. This is the north star for proactive, resilient cybersecurity. And we’re much closer to this perfect world than we may realize because the building blocks are all there.
Those building blocks are anchored in the fundamentals we all know. Every endpoint with EDR. Every app behind SSO. Every admin with MFA. Every known asset in the CMDB. Each of these fundamentals is declared as an invariant – conditions that should always hold, everywhere, all the time. Every security team designs for them on day one. And every security team discovers that declaring them is the easy part. Proving them continuously, across hundreds of thousands of assets, multiple environments, overlapping tools, and constant change – that's where the real work lives.
Now, AI has expanded our attack surface and the fundamentals we hold close. During the talk, I mentioned a few new considerations – every agent needs a defined auth scope, every non-human identity needs to be discovered and owned, every agentic workflow needs guardrails, and every AI tool in use needs to be known. But these aren’t a departure from the fundamentals we know - they follow the same pattern.
Security practitioners already have the muscle memory and chops to manage and control deterministic systems and probabilistic behaviors. AI introduces new flavors of both at a different speed and scale, but the discipline is the same. One key takeaway for the audience is that as a security community, we’re prepared for this.
Fragmentation is holding us back
The perfect world is within reach, but there is one thing holding us back: fragmentation. We all run different tech stacks; there’s no one-size-fits-all. And every system, tool, and application reports its own version of the truth based on what it sees and understands.
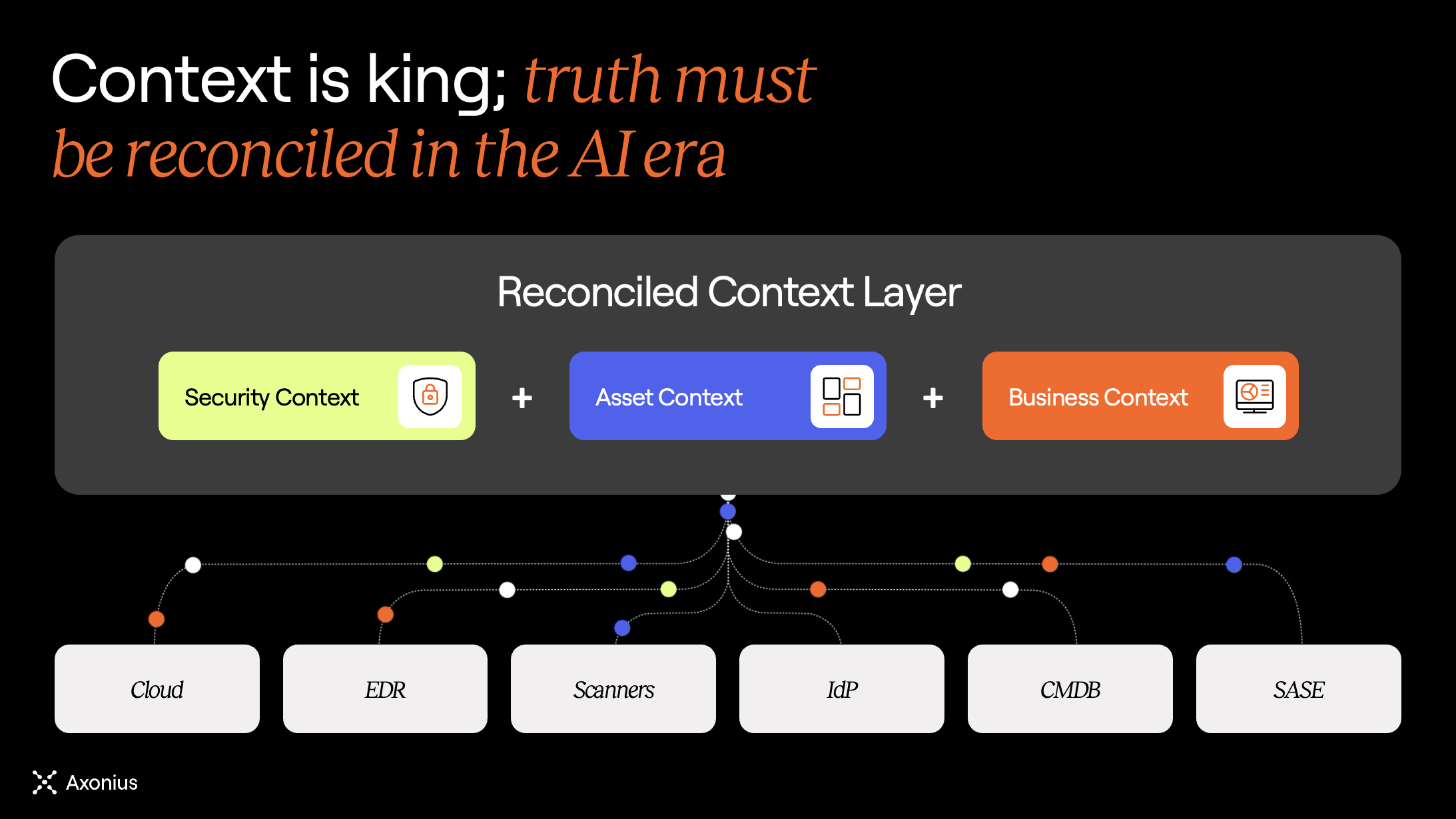
Your cloud provider sees ephemeral instances but is blind to the software running inside them. EDR knows about its agents but can't see the unmanaged resources surrounding them. A scanner detects vulnerabilities where it’s running, but is blind to the rest of the environment. When it comes down to it, no single system of record is the one source of truth. When these systems inevitably disagree, teams burn time reconciling the differences manually before they can take any action.
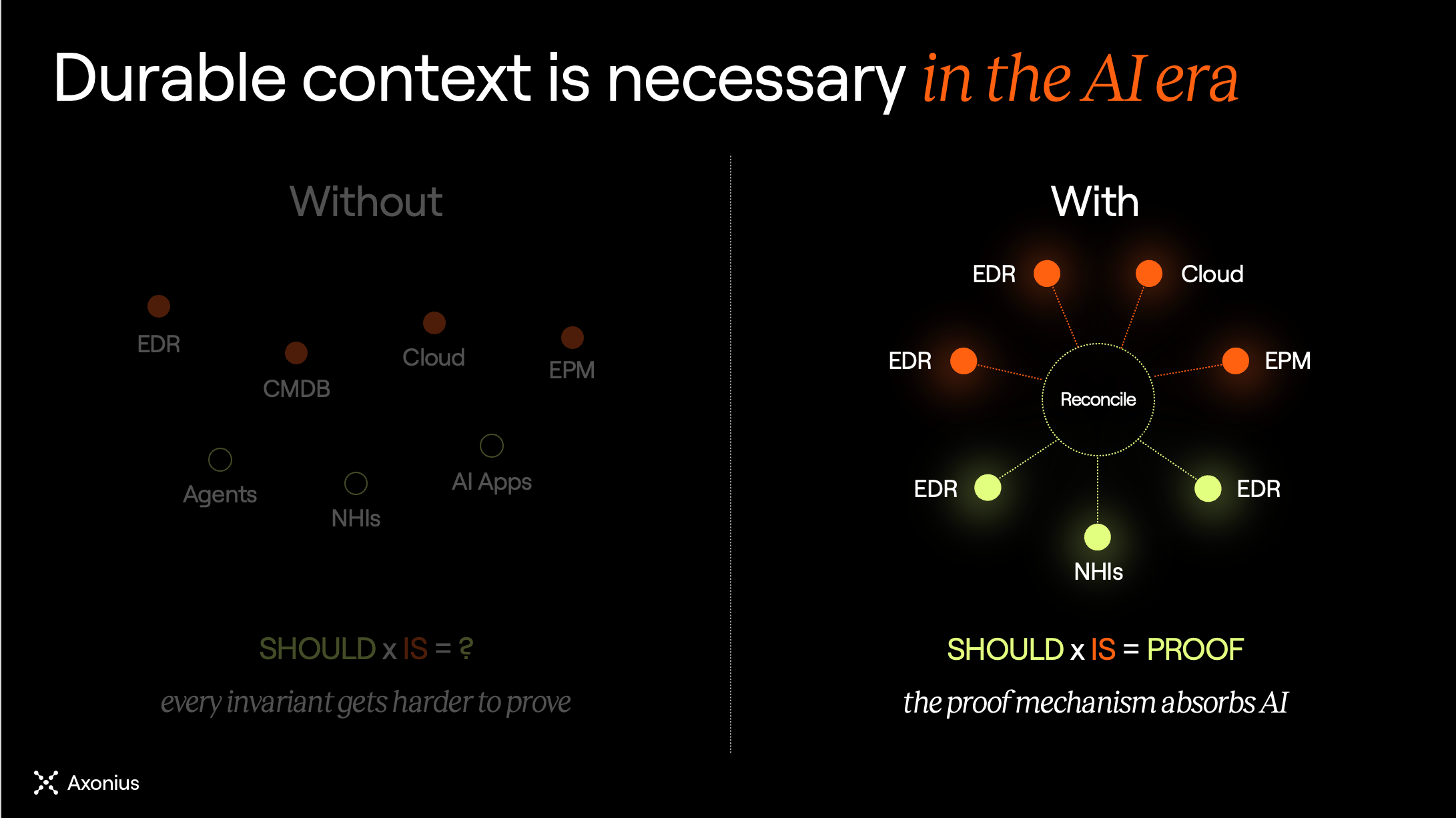
The fundamentals we hold close have always run on context. And now AI runs on context. Every scenario depends on knowing what exists, how it’s configured, who owns it, and what is its state. Without that, every declared invariant can’t be proven. To solve the fundamentals of the past, present, and future, we need durable context. Context that’s been reconciled, not just aggregated. Context that is always complete, accurate, and up-to-date as the environment changes.
There's an important distinction here. Aggregation collects partial truths and stacks them. Reconciliation resolves them: correlating records across sources, normalizing naming and schema differences, deduplicating where tools overlap, enriching with ownership and business context, and modeling the relationships between assets, identities, and exposures. The output is a single verified model of what's actually true. That's the bar for durable context. The bar we’ve set for ourselves as decision-grade asset intelligence.
Clearing the path to actionability
This is what we've been building at Axonius in the seven years since we first stood on the RSAC stage. Asset intelligence across our now 1,400+ bi-directional adapter integrations is the method that turns fragmented system state into environment-wide durable context. We correlate, normalize, deduplicate, enrich, and model asset and exposure data from every tool in the stack, continuously. The result is a reconciled context layer that security and IT teams can trust and act on, regardless of which tools sit underneath.
With durable context as the foundation, every fundamental becomes a durable function in the talk. A policy is a claim. An invariant is a claim with continuous proof. That’s the goal. The proof structure follows a simple pattern: What should be true versus what is true. The comparison gives you a binary, continuous answer.
Durable functions unlock actionability. Drift gets detected. Impact gets evaluated. Fixes get coordinated. Results get verified. Actionability follows a self-healing rhythm grounded in truth – declare, detect, decide, deliver.
And that's how we get to the perfect world we started with. It starts with the truth. It multiplies with actionability.
Categories
- Axonius News

Get Started
See how to make asset intelligence actionable with a guided demo:
- Stop chasing data — work from one asset model your entire team can trust.
- See what's exposed before it's a problem — surface coverage gaps automatically.
- Turn alert noise into action — cut thousands of alerts down, to the ones that matter.
