Forrester’s Proactive Security Landscape and the power of context
.png)
The surface area of risk has expanded. Forrester’s newly released The Proactive Security Platforms Landscape, Q1 2026 (PSP Landscape) notes disparate signals from attack surface management, traditional vulnerability management, and application and cloud security, to name just a few. This fragmentation is complicated by a deeper problem: a lack of trustworthy visibility into all assets and their ownership. This creates immense operational friction and drag on security programs. When you don't know what exists or who is responsible for it, making sense of siloed alerts is impossible.
Axonius is proud to be included amongst the “Notable Vendors” in Forrester’s PSP Landscape. The report notes that proactive security platforms must converge these disparate sources to deliver the context that teams are missing. The timing couldn’t be better as it goes hand-in-hand with our newly published 2026 Actionability Report, which confirms this friction.
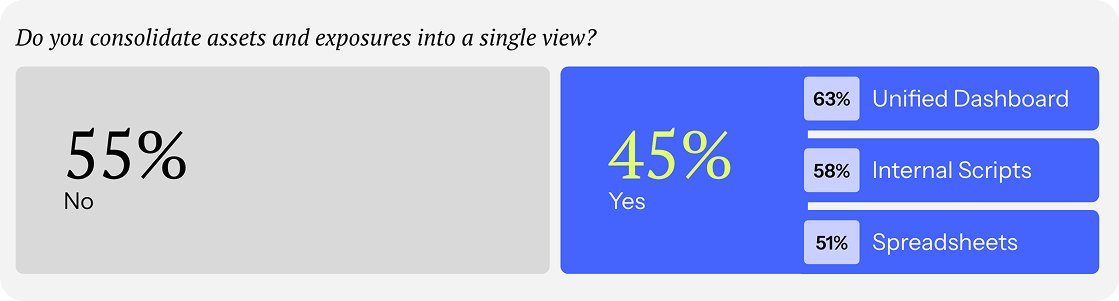
While teams have plenty of data, only 45% successfully consolidate assets and exposures into a single view. True proactive security requires an aggregation-first architecture. You need a decision-grade foundation of assets and owners to make sense of the noise and eliminate operational drag before you can act.
You can't prioritize what you can't trust
Forrester highlights asset and exposure inventory as a core use case, serving as the single source of truth for technology assets. Effective prioritization that reduces risk requires comprehensive visibility.
But these days, anyone can vibe code an API connection and claim visibility. The real bar is durable context. Workflows are unblocked when grounded in verifiable truths. And the future possibility of self-healing environments will absolutely require these truths to function. Security invariants, the things that should be true and must be proven to hold true, require accounting for both what is there and the negative space of what is not. Only a durable context layer meets this decision-grade bar.
This foundation is realized through the Axonius Asset Cloud, where Cyber Assets provides the authoritative model. Our adapter network connects 1,400+ systems, but the real power is how it reconciles every asset across your stack into one authoritative, decision-grade model. When asset intelligence acts as the proof of your invariants, you eliminate the friction of debating what exists and who owns it. You stop arguing over spreadsheets and start acting on facts.
Doug Graham, Chief Trust Officer at Lionbridge, validates this approach: "Axonius provides us with a single source of visibility and a single source of truth. We're no longer arguing about what's there and what's not there, what's been patched and what's not been patched, and what coverage looks like."
Why CVSS scores aren't enough to prioritize risk
Forrester notes that prioritization strategies have shifted beyond CVSS scores to incorporate deeper context across the evolving attack surface. The industry lags behind this ideal, creating massive triage friction. Our research found that 56% of organizations still rely primarily on blunt scoring systems like CVSS to drive prioritization.
.png)
Axonius Exposures breaks the silos by correlating technical findings from 150+ security tools with deep asset and business context. The result: a list of 1,000 critical security findings becomes the 100 (or 50) that actually threaten the business.

As the Head of Information Security at a large university noted: “The main challenge was we were getting too many vulnerabilities, and so we had difficulty prioritizing them... What we now focus on is probably five to 10% of what we told remediators to worry about in the past.”
Remediation without coordination is just a to-do list
A prioritized list of problems, in and of itself, doesn't improve security posture. Forrester states these platforms must also be the basis for how the response is coordinated. Yet, coordination remains highly manual for most programs. According to our Actionability Report, 55% of organizations still track remediation progress in spreadsheets.
Axonius doesn't just read from your tools; we write back. By automating owner identification and routing "ready-to-work" tickets to the systems teams already use, Axonius serves as the mobilization engine for remediation. This removes the operational drag of manual chasing and detective work that stalls remediation for weeks, driving measurable reductions in Mean Time to Remediate (MTTR).
Achieving zero drag in your security program
Proactive security requires achieving zero drag. By reconciling the disparate data you already have, you can proactively contextualize with clarity, decide with confidence, and act with precision (instead of dragging on silos and working reactively).
- Read the Forrester Proactive Security Platforms Landscape, Q1 2026 report to see how the market is evolving.
- Read Axonius’ 2026 Actionability Report and see the data on why teams struggle to move from visibility to action.
Categories
- Axonius News

Get Started
See how to make asset intelligence actionable with a guided demo:
- Stop chasing data — work from one asset model your entire team can trust.
- See what's exposed before it's a problem — surface coverage gaps automatically.
- Turn alert noise into action — cut thousands of alerts down, to the ones that matter.
